What gets written to the log file is determined by the configuration of your log sink.
By default, the ssg log sink includes both "Category=Audits" and Category="Gateway Log" with no additional filters.
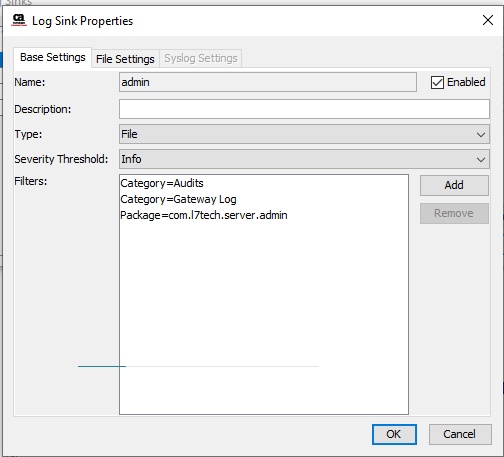
If you want a log with just admin activities (in the logs as com.l7tech.server.admin) including log in/outyou could try a log sink like below. In my testing it gets the login and logout events, and other admin events.
Keep in mind that your log.levels Cluster Wide Property plays a big role in what actually hits the log sinks. For example if you had modified it and set "com.l7tech.level = Warning" the log in/out messages would never reach the log sink filters. In that case you would need to add a log.levels line like "com.l7tech.server.admin.level = INFO" to ensure those messages make it to the sink.
I hope this makes sense?
Original Message:
Sent: Feb 27, 2025 03:27 AM
From: Kuldeep H
Subject: To capture user related activities (login/logout) in separate log files
SSG logs are combination of application bootup/api request/response & processed logs and other events performed at gateway store in a common log file such as ssg. We are looking for solution to capture only use login/logout information (also login through LDAP authentication) and user changes such as create/update/delete to a separate log file which should contain these information. Team, Please provide your view on this topic.