Hi Teja,
I was able to replicate the issue in my lab.
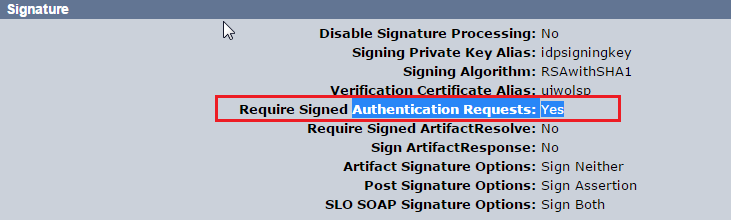
It seems that you have Signed Authentication request requirement set to YES at IDP :
However, the AuthnRequest sent by SP is not signed.
You can verify this by reviewing the fiddler. If the AuthNRequest is signed you should see the signature as below :
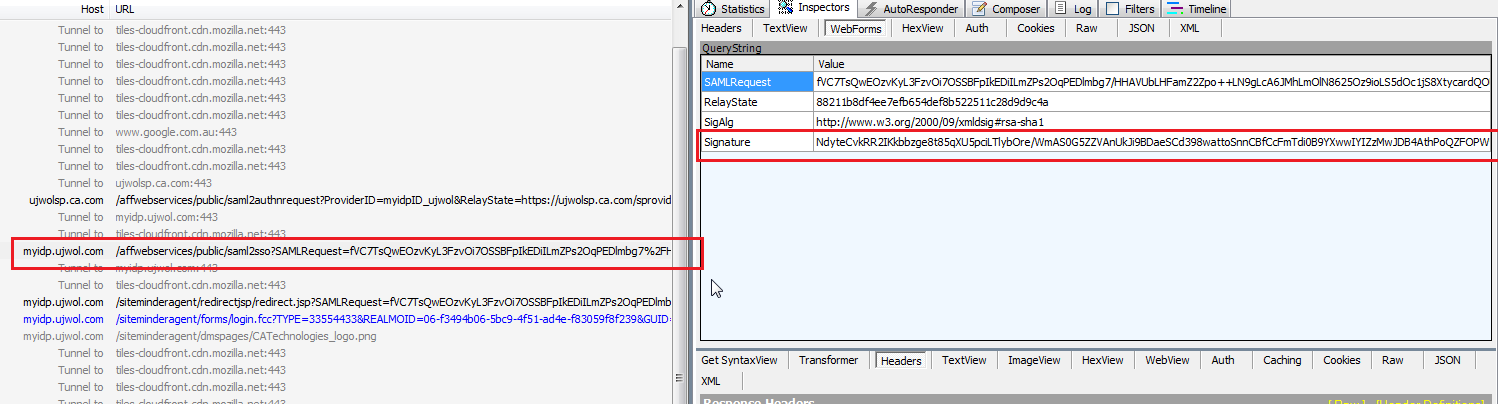
Fig. Signed AuthNRequest
In case of unsigned AuthnRequest , you will NOT see the Signature , see below :

Fig. Un Signed AuthNRequest
Also, if you have the detailed tracing enabled on Policy server you should see the exact error message like this on IDP smtrace log :
[11/21/2016][10:35:05][4788][a15a8888-d72d7f92-b17b0803-fc600ef2-0050a3e4-d3][AuthnRequestProtocol.java][verifySignatureOnRequest][][][][][][][][Authnrequests are required to be signed but the request did not contain a required query parameter: Signature, or SigAlg is missing.]
[11/21/2016][10:35:05][4788][a15a8888-d72d7f92-b17b0803-fc600ef2-0050a3e4-d3][AssertionGenerator.java][invoke][][][][][][][][AssertionHandler preProcess() failed. Leaving AssertionGenerator.]
Solution :
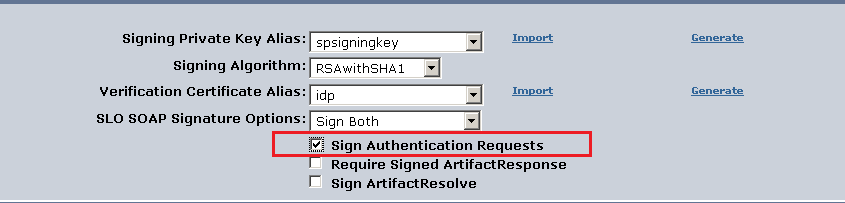
Configure SP to sign AuthNRequest. If SP is CA SSO you can do this as below on SP side of partnership :
Let me know if this works for you.
Regards,
Ujwol Shrestha
Ujwol's Single Sign-On Blog