
A new variant of Android ransomware (Android.Lockdroid.E) takes advantage of Google’s Material Design and an open-source project to create the lockscreen’s user interface (UI). This allows the threat to easily display fraudulent legal notices and gathered device logs to make the ransom notice seem more intimidating.
The ransomware isn’t spreading through the Google Play store. Instead, a device can be compromised in one of two ways:
- The user downloads a free software package on their computer which includes a popular browser hijacker. This hijacker then redirects the victim's search results to sites hosting the Android ransomware.
- The ransomware is disguised as a legitimate video app and is made available on unofficial app stores.
What is Material Design?
Material Design is a design language developed by Google and was first introduced in 2014. The system uses grid-based layouts, responsive animations, depth effects, and spacing to provide a unified user experience across all of the company’s services. Third-party developers can apply this style to their own apps using Google’s resources and open-source projects.
How Android.Lockdroid.E uses Material Design
The authors of Android.Lockdroid.E implemented Material Design to create a lockscreen with a cleaner, more professional-looking UI. The malware also used this design language to display the personal data that it gathers through an easy-to-access menu. These elements help the ransomware intimidate the victim into making the payment.
Once the Trojan compromises a device and is executed for the first time, it collects all logs available at that point in time, including call records, SMS activity, and browser history. The threat then locks the device from use, displaying a ransom notice on the lockscreen which claims that the user has accessed prohibited content and that their device logs are in law enforcement’s custody. The threat then includes the gathered log data as options in the lockscreen’s menu, which is supposed to act as “proof” of the user’s illegal behavior.
The following image shows how the ransomware’s lockscreen uses Material Design. The victim can slide the left-side app drawer on screen or select the menu icon to access a list of the lockscreen’s options.

Figure 1. Left-side app drawer’s menu
The options include the ransom notice, fraudulent legal information, and the gathered log data. This was made available to back up the attackers’ claims of the victim’s “illegal activity.”
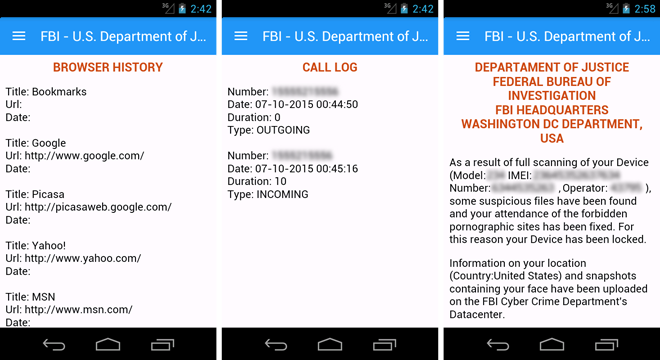
Figure 2. Lockscreen’s menu includes browser history details, call log data, and a fraudulent legal notice
Other ransomware families have been observed gathering the logs of SMS activity, call records, and browser history in the past. However we haven’t seen ransomware threats that make these logs more accessible to the victim through Material Design before.
How did the attackers create their UI?
The malware variant’s authors used a popular open-source project called MaterialDrawer to build part of the lockscreen’s ‘Material Design’-based UI.
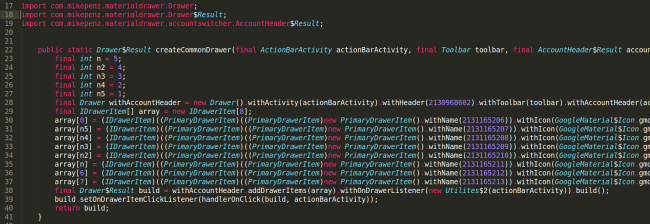
Figure 3. Code snippet of the lockscreen’s left-side app drawer
It should be noted that MaterialDrawer’s creators did not intend for their work to be used for malicious purposes. The authors of this ransomware simply accessed and used the layout as any other legitimate app developer would.
Mitigation
Symantec detects this ransomware as Android.Lockdroid.E and recommends the following security best practices:
- Keep your software up to date
- Refrain from downloading apps from unfamiliar sites
- Only install apps from trusted sources
- Pay close attention to the permissions requested by an app
- Install a suitable mobile security app, such as Norton, in order to protect your device and data
- Make frequent backups of important data