Some of the key takeaways from August’s Latest Intelligence, and the threat landscape in general, include increases in the email malware and spam rates, new ransomware functionalities, and new phishing warnings from the IRS.
Malware
The email malware rate increased slightly in August, up to one in 347 emails. The email malware rate has increased slowly, but steadily, since April. The return of the Necurs botnet around this time likely played a pivotal role in this increase, following the decline in the email malware rate seen from January through March of this year.
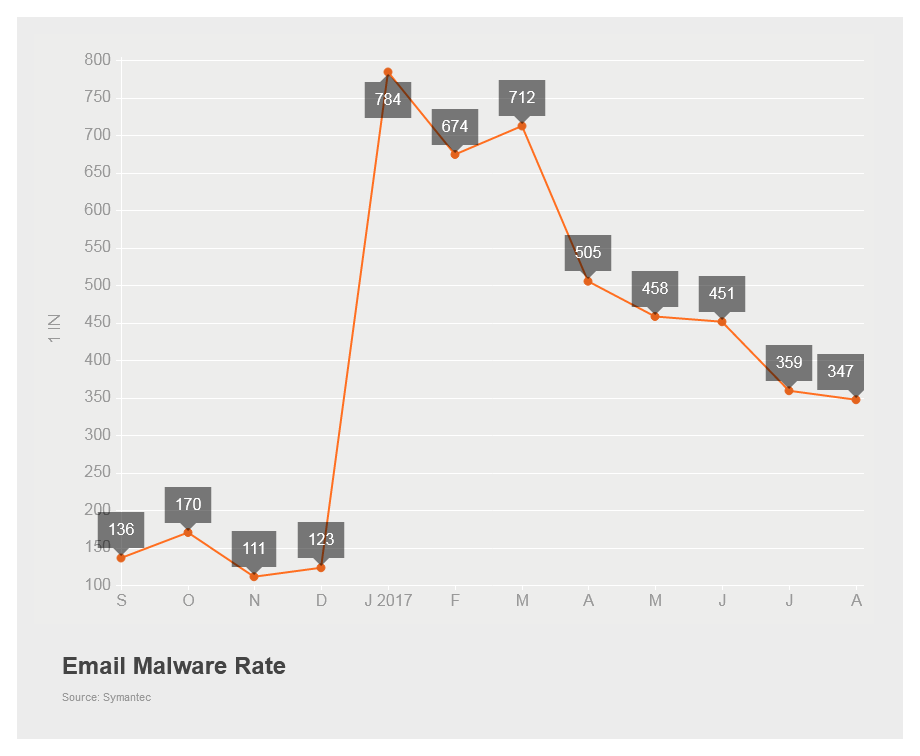
Figure 1. The email malware rate increased slightly in August
One of the payloads distributed through Necurs was found to contain new functionality in August. A variant of the Cerber ransomware family (Ransom.Cerber) was discovered that attempted to steal Bitcoin wallets from compromised computers. However, stealing these wallets didn’t give the attackers the ability to empty them, since a password is needed to open the wallets.
In order to address this issue, it appears as though the attackers attempted to gather saved passwords from popular web browsers on the comprised computers, in the hopes that the passwords users had stored there may have been reused in the bitcoin wallets, thus allowing the attackers to open them and take the bitcoins stored within.
Spam
The global spam rate increased for the third month in a row and comprised 55.3 percent of email sent during the month of August. This once again sets a record for the year and marks the highest spam rate seen since March 2015.

Figure 2. The spam rate incresed to its highest level so far this year in August
A massive spambot uncovered during August was found to contain approximately 711 million email addresses. The bot, named Onliner (Backdoor.Oliner) by security researchers, also appeared to have stolen SMTP credentials in order to bypass email filters and make it appear as though the emails were coming from legitimate sources. The spambot was distributing variants of the Snifula family of information stealing Trojans (Infostealer.Snifula).
Phishing
The phishing rate declined slightly in August, to one in 2,493 emails. This follows five months of increasing phishing rates, which reached a 12-month high in July. Phishing rates also decreased across industries and organizations of all sizes.
The IRS warned users of a new phishing scam discovered in August that had the goal of stealing client information from tax professionals. The scam took the form of emails that appeared to come from tax software providers and claimed that the user must revalidate their login credentials on the company website. However, the link contained in the email pointed to a fake login page that mimicked the company’s website. The fake website stored user names and passwords if a tax professional entered them, and these could then be used to access client information.
Web Attacks
The number of web attacks blocked increased slightly in August, up from 1,159,000 per day to 1,241,000 per day. This follows slight web attack declines over the last two months, but overall August marks five months of elevated web attack activity.
Mobile
While there were no new Android malware families discovered in the month of August, it appears as though it is getting easier for attackers to create mobile malware. In particular, a Trojan Development Kit (TDK) was uncovered that allows an attacker to simply fill out an on-screen form in order to create ransomware. While the distribution of the newly created threats is left up to the attacker, any user who unwittingly installs the threat will end up with their device locked for ransom. The Trojans created by these TDKs are detected as Android.Lockdroid.E.
This is just a snapshot of the news for the month. Check out the Latest Intelligence for the big picture of the threat landscape, with more charts, tables, and analysis.