Backdoor.Egobot is a Trojan used in campaigns targeting Korean interests. The execution of the campaigns is straightforward and effective. Symantec data indicates the campaigns have been in operation since 2009. Egobot has continuously evolved by adding newer functionalities. The attackers use the four golden rules of a targeted campaign:
- Identify targets
- Exploit targets (in order to drop the payload)
- Perform malicious activity (in this case, stealing information)
- Remain undetected
We have also uncovered a parallel campaign that has been in operation as early as 2006, which we will cover in another blog.
Egobot targets
Egobot is targeted at executives working for Korean companies and also at executives doing business with Korea. Industries targeted with Egobot include:
- Finance and investment
- Infrastructure and development
- Government agencies
- Defense contractors
Targets are located around the globe and include Korea, Australia, Russia, Brazil, and the United States.

Figure 1. Countries targeted with Backdoor.Egobot
The aim of the Egobot campaign is to steal confidential information from compromised computers.
Exploitation
The attackers gather information about their targets using social engineering techniques prior to luring them into the trap. The targets are sent a spear phishing email, often pretending to be sent from a person they already know. The spear phishing email contains a relevant or enticing message to the target, prompting them to open the malicious attachment. The malicious attachment may be a shortcut .lnk file that points to a file hosted on GeoCities Japan.
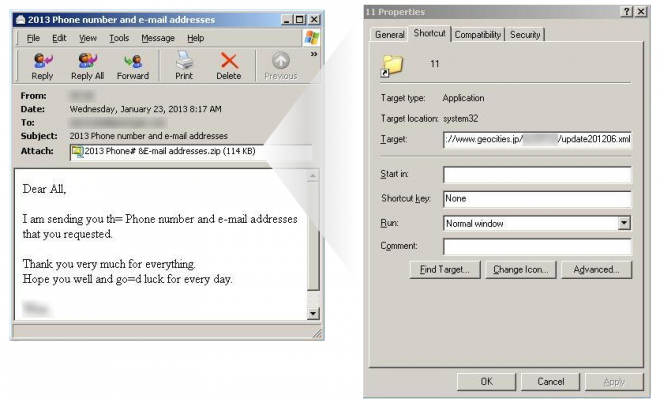
Figure 2. Egobot spear phishing email with malicious shortcut attachment
Various malicious attachments have been used in this campaign:
- .Lnk files: We have seen this tactic used before, however, these attackers also use Microsoft’s HTML Application (MSHTA) to download another file onto the system.
- .Doc files: Exploits the following vulnerabilities:
- .Hwp files: Contains script that downloads a malicious file
When attachments are opened it triggers the following three-stage download process:
Stage 1: Download obfuscated HTML file
Each of the attachments downloads malware from sites hosted on GeoCities Japan. The files vary, but are usually named update[YYYYMM].xml which is an obfuscated HTML file that drops an executable on the system.
Stage 2: Download RAR archive
The dropped executable from Stage 1 then retrieves another file from GeoCities Japan. This file is hotfix[YYYYMM].xml, which is an executable RAR file. Both downloaded files in the first two stages are disguised as XML documents in an attempt to pass as a clean file.
Stage 3: Download back door component
The executable RAR file is responsible for preparing the system. It drops a set of files which are responsible for moving files around, injecting a component into processes, and stealing the following system information:
- Windows version
- Installed service pack version
- Install language
- User name
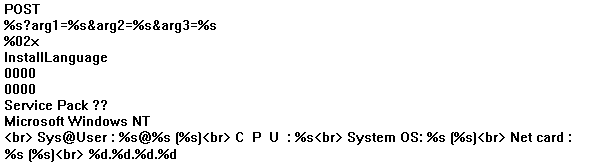
Figure 3. Stolen system information found in Egobot strings
Stolen information is sent to Egobot's command-and-control (C&C) server in the following format:
- /micro/advice.php?arg1=1irst&arg2=[BASE64 ENCODED STRING]
- /micro/advice.php?arg1=1irst&arg2=[HASH]&arg3=[BASE64 ENCODED STRING]
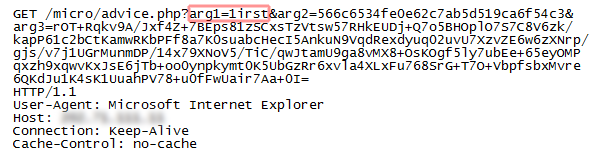
Figure 4. Communication back to C&C server, arg1 value highlighted
Data that is sent back to the C&C is encrypted using a rotating key embedded within the malware. We observed the following two specific keys:
- youareveryverygoodthing
- allmyshitisveryverymuch
Finally, the executable RAR file downloads one last component from GeoCities Japan. This downloaded file is named using the value of arg1 in the GET command sent to the C&C. In this case, Egobot attempts to download a file called 1irst.tmp, which is the main payload.
Stealing information
The main payload has specific functions that are potentially disastrous for targeted business executives. These functions include:
- Recording video
- Recording audio
- Taking screenshots
- Uploading files to a remote server
- Obtaining a recent document list
- Searching for a string or pattern in a file
- Deleting and setting restore points
The stolen information is uploaded to remote servers hosted in Malaysia, Hong Kong, and Canada. The attackers have also updated their code to include 64-bit versions to work seamlessly across 64-bit platforms.
Staying under the radar
Egobot is downloaded onto a system as a bundled RAR archive with various components packed using commercial packers exe32pack and UPX. These following components are used to mask the presence of the malware:
- Detoured component: Backdoor.Egobot is compiled using an older version of Microsoft's Detours software package functionality, which includes the detoured.dll file. This file is used to attach malicious .dll files to legitimate Win32 binaries. Egobot can use this file to run itself in the memory of a legitimate process, masquerading as a clean process.
- Coordinator component: Prepares files by moving them into the appropriate folders and injecting them into legitimate processes. Backdoor.Egobot is typically injected into the explorer.exe, subst.exe, and alg.exe processes.
- Timer functionality: Some versions of the back door component include a timer functionality so the Trojan can delete itself after a certain date. This feature removes any traces of Backdoor.Egobot.

Figure 5. Backdoor.Egobot components
Symantec customers are protected by Symantec Email Security.cloud. Malicious samples from this campaign are detected as Trojan Horse, Trojan.Dropper, Trojan.Mdropper, and Backdoor.Egobot.
And, unfortunately, there is more to this story. Through our research into Egobot, Symantec has identified a parallel operation related to Egobot that has been active since 2006, about three years before Egobot. Further details on the Nemim campaign—including its relation to the Egobot campaign—are explained in a separate blog, Infostealer.Nemim: How a Pervasive Infostealer Continues to Evolve.