More than 2,500 Twitter accounts have been compromised to tweet links to websites specializing in adult dating and sex personals. The attackers also changed the profile photo, biography, and full name of the accounts to promote these sites. It’s likely that the attackers earned money by redirecting users to these sites through affiliate programs.
During our investigation into this campaign, we found a few notable compromised Twitter accounts belonging to electrofunk band Chromeo as well as an international journalist from The Telegraph. In addition to our investigation, recent reports found that the Twitter accounts of stand-up comedian Azeem Banatwala, Houston Texans wide receiver Cecil Shorts III, and the late New York Times reporter David Carr were also compromised.

Figure 1. Electrofunk band Chromeo’s Twitter account was compromised as part of the scam
The curiosity factor: Liking tweets and following users
Rather than tweeting or direct-messaging users, the attackers used these compromised accounts to like tweets and follow other users, hoping to capitalize on users being curious enough to investigate their Twitter profiles.

Figure 2. Compromised profile likes tweets of legitimate users
If a user visits the compromised profile, they will see tweets that claim to offer free sign-ups to watch “hot shows” over webcam, or dates and sexual encounters. Each of these tweets includes sexually suggestive photos and shortened links using either Bitly or Google’s URL shortener, goo.gl.
Adult dating and sex personals
The shortened links lead to an intermediate landing page, advertising an adult dating/sex personals website.

Figure 3. Adult dating/sex personals landing page
If the user clicks through the prompts on the landing page, they are redirected to the actual site. This redirect includes an affiliate tag to identify where the traffic originated from.
The adult dating website linked to in this campaign incentivize people to drive traffic to their sites. They do this through affiliate programs that pay people for getting users to sign up. Based on our research, we believe the affiliate involved in the Twitter account compromises would earn US$4.00 for each person who signs up for the website.
Compromised accounts
We noted the following while investigating the compromised Twitter accounts:
- The profile photo, biography, and full name were changed
- Recent tweets contain suggestive images and language discussing adult webcam sessions and sexual encounters
- Historical tweets, location, URL, and header image (if set) remained intact
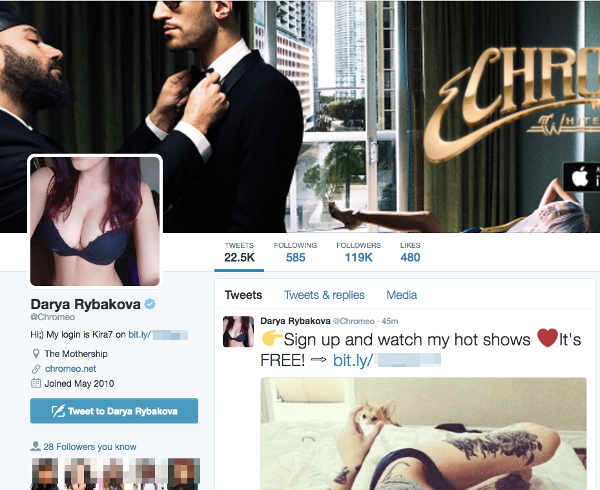
Figure 4. Compromised profiles include a new profile photo and description
The original profile photo is often changed to a photograph of woman, typically in a suggestive pose or wearing lingerie/swimwear. However, some compromised accounts maintain the original profile photo or, in some cases, use the default “egg” avatar associated with new Twitter accounts.
In addition to the changed profile photos, these compromised accounts alter the profile biography and full name. Recent examples include the message “Hi!;) My login is [RANDOM NAME AND NUMBER] on [SHORTENED URL]”. The names appear to be real names extracted from other sources.
Old is gold
During our investigation, we identified more than 2,500 compromised Twitter accounts. Some data points about these compromised accounts include:
- The oldest account was registered in December 2007
- 27 percent of the compromised accounts were created in 2011
- 73 percent of the compromised accounts are at least four years or older
- Many of the older accounts were orphaned by their owners and have not sent any new tweets in years
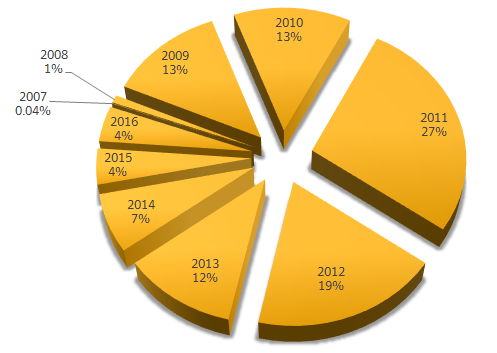
Figure 5. Creation dates of compromised accounts. Most of the accounts are at least four to five years old
Secure your Twitter account
If you’re an active Twitter user and you are concerned about your account being compromised, there are a few things you can do to secure your account:
- Create a strong and unique password: It is likely that many of the compromised accounts used weak passwords or re-used passwords on other services.
- Use a password manager: If you want to create and securely store your passwords, we suggest using a password manager. While there are plenty to choose from (LastPass, 1Password, Dashlane, KeePass, Password Safe, Norton Identity Safe), we suggest you use one that best meets your needs and your budget.
- Consider enabling Twitter’s Login Verification: Instead of relying on just a password, Login Verification requires you to enter a code that is sent to your mobile phone. This adds an extra layer of security and helps prevent unauthorized access to your account. Just be sure to securely store your backup code in case you lose your mobile phone.
Report compromised accounts to Twitter
If you believe that someone you know or follow has been compromised, you can report their account to Twitter by selecting the gear icon on their profile and clicking on Report. From there, select the option “Their account may be hacked” to proceed.

Figure 6. Reporting a hacked account to Twitter
We notified Twitter, Bitly, and Google, and provided data on the accounts and shortened URLs used by these accounts.
Update – May 25, 2016: Symantec continues to see newly compromised accounts, including the following notable accounts:
- OptionAction (CNBC television show)
- Paula Newton (CNN correspondent)
- XO Stereo (Los Angeles based band)
- Anne Marie Owens (Editor-in-chief of the National Post)
- Kristen Kennedy (Weekend anchor at WKYT)