
Some Dell computers are vulnerable to man-in-the-middle attacks because of an issue with a root certificate authority. This problem is reminiscent of SuperFish, which affected Lenovo computers earlier this year and left them similarly vulnerable. SuperFish allowed for man-in-the-middle attacks that could let an attacker snoop on (what were thought to be) secure communications.
The problem with Dell computers was discovered by Joe Nord, who pointed to a certificate named eDellRoot which was valid through 2039:

Figure 1. eDellRoot certificate authority problem discovered by Joe Nord
Dell installs a self-signed root certificate authority, eDellRoot, on a number of their computers, along with, critically, the private key. As the name implies, the private key should not be made public. This same private key has been used across a number of Dell computers, and it has since been exposed. This can allow attackers to perform man-in-the-middle attacks on the affected computers.
In addition to man-in-the-middle attacks, the eDellRoot certificate authority and private key can also allow attackers to sign code. This means that attackers can sign malware as if it was from another company, but it will look legitimate to computers with the eDellRoot certificate authority installed. This can allow attackers to easily masquerade as legitimate software on Dell computers affected by this issue. Malware signed with the eDellRoot certificate authority has already started appearing on VirusTotal.
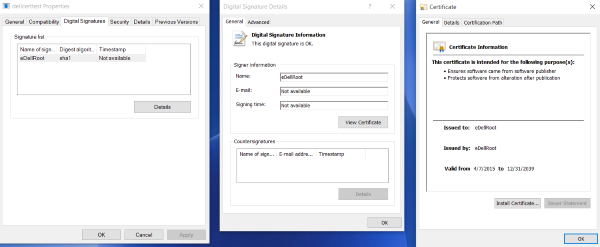
Figure 2. File signed with the eDellRoot certificate
Symantec tested Dell computers and found that the eDellRoot certificate authority was present on the following models:
- Inspiron 7000 (laptop and desktop)
- Dell Orchid Touch
- Dell t4034
Some users have also reported that Asus computers have the certificate installed, but Symantec was unable to independently verify the claim.
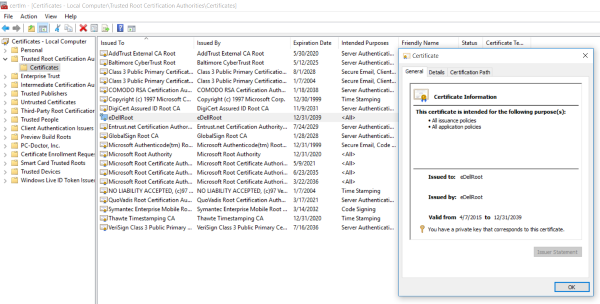
Figure 3. Dell Inspiron 15 7000 laptop with eDellRoot certificate authority installed
Dell addressed the issue and acknowledged that the eDellRoot certificate, “unintentionally introduced a security vulnerability,” on the affected computers. The company also provided removal instructions to correct the problem and will be issuing a software update to check for the certificate and remove it, if present. If the certificate is not removed using Dell’s instructions, it can be reinstalled when the affected computer is rebooted.
Update – November 25, 2015:
An additional root certificate, DSDTestProvider, has also been found on Dell computers. This certificate poses a similar threat as the eDellRoot certificate.
Mitigation
Users can revoke the DSDTestProvider certificate by launching the Windows certificate manager ("certmgr.msc") and moving the DSDTestProvider certificate from the Trusted Root Certificate Store to Untrusted Certificates.