
Last month, we blogged about some of the detection-evasion and anti-analysis tactics employed by Android ransomware and the continuous cat-and-mouse game between the security community and ransomware creators.
In this blog, we will look at how the Android platform continues to evolve, and in particular how recent changes in Android 6.0 Marshmallow could have a potential impact in the mobile malware ecosystem. Google is due to release the final version of Android 6.0 before the end of September, so these changes may arrive on users’ phones sooner rather than later, depending on their device manufacturer or carrier.
Let’s discuss some of the concepts that will help us understand how the upcoming OS update may affect mobile ransomware.
How does ransomware work in Android?
While there can be more than one answer to this question, the most common trick seen in almost all of Android ransomware variants is to leverage the “SYSTEM_ALERT_WINDOW” permission in order to lock infected devices’ screens. The threats largely depend on this permission, as it allows an application to open system-type windows and display them on top of every other application or window.
As the following image shows, a device infected with Android.Lockdroid.E displays a WebView—a view that displays web pages—in a linear layout, with the layout type set to “TYPE_SYSTEM_ALERT” to create a system-alert type of window.

Figure 1. Layout properties (left) set to “TYPE_SYSTEM_ALERT” would create a system-alert type of window (right), locking the device
Alternatively, certain Russian-language ransomware variants tend to use “system error” or “system overlay” type of windows, which can also superimpose themselves over all other windows displayed on the device, as shown in Figure 2.
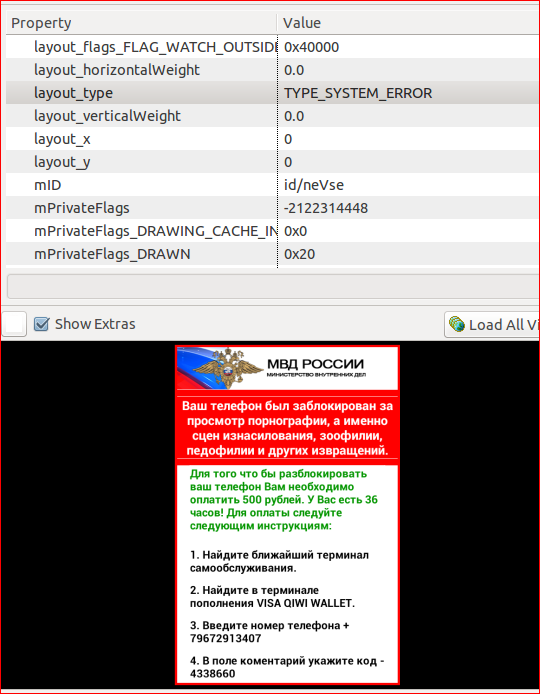
Figure 2. Russian-language ransomware usually locks a device’s screen using a system-error type of window
In general, ransomware variants use system-type windows—system alert, system error, or system overlay—to create locked screens that can appear on top of all other windows.
In Android, if any app is trying to create a system window, it must get “android.permission.SYSTEM_ALERT_WINDOW” from the user of the device.
Change is afoot
Now, ransomware creators who decide to create malware with Android Marshmallow as their target will have their work cut out for them. Given the new changes in the latest version of the OS, which is due to be released sometime this month after the third and final preview was released on August 17, ransomware creators are bound to run into some difficulty. These changes are poised to challenge ransomware that relies on obtaining the permissions outlined previously, thereby limiting its ability to lock screens.
Starting with this new version of Android, a new permissions model will be in force, where apps will be required to request permissions on an as-needed basis. Device owners will now be prompted whether to approve, on demand, when an app tries to use a feature that needs permission from the “dangerous” category (as set by Android developers).
Besides that hurdle for creators of malicious apps, they face an even bigger obstacle, as the final Mashmallow software development kit (SDK) has already placed the permission “SYSTEM_ALERT_WINDOW” in the “above dangerous” category.
This means that if a ransomware app has set its target SDK as Marshmallow, it will need explicit permission from the user to lock their device. For a user to give this permission, they need to manually navigate through not-so-straightforward steps from the Settings app before they can allow the app to lock the screen.

Figure 3. Permissions that can simply be turned on/off on an app’s permissions tab

Figure 4. “Above dangerous” permissions are hidden inside the Settings screen and will require a user to go through several steps to grant them
Backward compatibility
Does this development mean Android ransomware is on the brink of extinction? No, certainly not. While the changes are a really good move on Android’s part, ransomware creators could, and likely will, update their code to directly take the victims to this Settings screen and use social-engineering tricks to convince them into turning on this permission.
More importantly, Android 6.0’s backward compatibility feature could provide another lifeline for ransomware to continue to infect devices running Marshmallow. The new permission model will only be applicable if the malicious app is specifically targeting the Marshmallow SDK. If the attacker targets a previous Android SDK (Lollipop, for example) their ransomware could still work on a Marshmallow device by following the older permission model.
Nevertheless, the new model is one more hurdle for ransomware creators to cross when Marshmallow is fully released.
Protection
Symantec recommends users to follow these best practices to stay protected from mobile ransomware:
- Refrain from downloading apps from unfamiliar sites and only install apps from trusted sources
- Pay close attention to the permissions that apps request
- Install a suitable mobile security app, such as Norton, in order to protect your device and data
- Keep your software up to date
- Make frequent backups of important data
Symantec and Norton products detect the threats discussed in this blog as: