A newly discovered vulnerability in the SSL and TLS cryptographic protocols could allow attackers to intercept and decrypt communications between affected clients and servers. Dubbed the “FREAK” vulnerability, it facilitates man-in-the-middle (MITM) attacks against secure connections where the server accepts RSA_EXPORT cipher suites and the client either offers an RSA_EXPORT suite or uses an older, unpatched version of OpenSSL. Once the encryption is broken by the attackers, they could steal passwords and other personal information and potentially launch further attacks against the website.
FREAK was discovered by a team of security researchers, who estimated that servers supporting just under ten percent of the top 1 million Alexa-listed domains were vulnerable to attack. Among the vulnerable client types were many Android and Apple devices, a high number of embedded systems, and a range of software products.
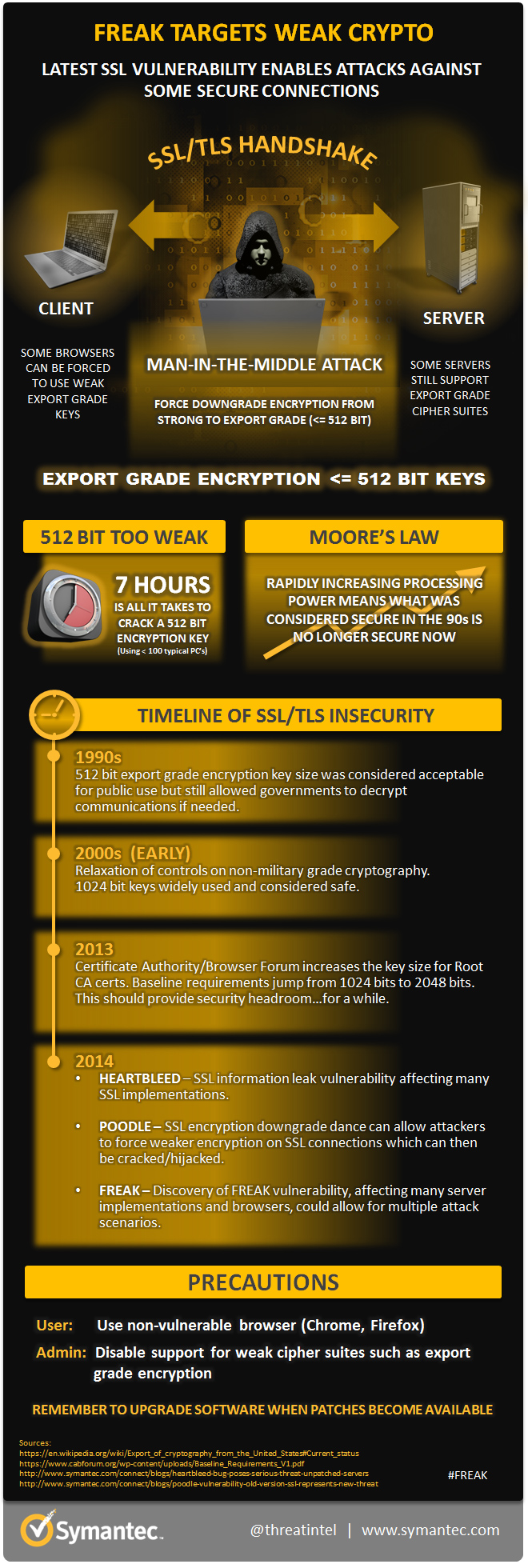
The vulnerability lies in the fact that attackers who intercept the setting up of a secure connection between an affected server and client can force them to use “export-grade” encryption in their communications, a much weaker form of encryption than is usually used today.
Export-grade encryption is so called because of a US government policy dating from the 1990s which required cryptographic software intended for export to use 512-bit encryption or less, which was not as secure as encryption used in the domestic market. While the policy has long been abandoned, export grade encryption has continued to exist as a legacy feature in a number of SSL/TLS implementations.
Even in the late 1990s, 512-bit encryption was seen as relatively weak and, by today’s standards, it is exceptionally so and can usually be cracked within a matter of hours. The standard was long ago superseded by 1024-bit encryption, which in theory would require millions of computers working for years to crack. Despite this, 1024-bit encryption was recently phased out in favor of the far more secure 2048-bit encryption to provide even more headroom.
Advice for businesses
Web server owners are advised to disable support for export grade encryption in addition to checking that any other known insecure ciphers are also disabled. Further guidance is available here.
OpenSSL users are advised to upgrade to the latest version, OpenSSL 1.0.2, which was released on January 22 and contains a patch for the OpenSSL Man in the Middle Security Bypass Vulnerability (CVE-2015-0204).
Advice for consumers
Users of Google Android devices who are concerned about this issue are advised to use the Chrome web browser rather than the default Android browser. Google has issued a patch and users are advised to update as soon as it is made available on their device.
Users of Apple desktop and mobile devices who are concerned about this issue are advised not to use the Safari browser until a patch is issued, which is due to arrive next week. Alternative browsers such as Firefox or Chrome are not affected by the vulnerability.
Additional information
Symantec has provided the following tool to verify whether or not a domain is vulnerable:
https://ssltools.websecurity.symantec.com/checker/
Update – March 6, 2015:
Microsoft has issued an advisory, warning that Secure Channel (also known as Schannel), the Windows implementation of SSL/TLS, is also vulnerable to FREAK attacks. Microsoft said that a security feature bypass vulnerability (CVE-2015-1637) in Schannel affects all supported releases of Windows. The vulnerability could allow an attacker to force the downgrading of the cipher suites used in an SSL/TLS connection on a Windows computer.
Users of Microsoft Windows who are concerned about this issue are advised to apply workarounds to disable the RSA export ciphers. Microsoft recommends for customers to use these workarounds to mitigate this vulnerability.
Symantec has released an Audit IPS signature (Audit: Weak Export Cipher Suite) to detect traffic from servers that accept export ciphers. As of now the signature is called “Web Attack: Weak Export Cipher Suite CVE-2015-00242” but it will be renamed to “Audit: Weak Export Cipher Suite” in the next IPS definitions release.
IPS Audit signatures are available in SEP 12.1 RU2 (released November 2012) and above. We recommend customers run our latest software version (SEP 12.1 RU5) as this contains further IPS Audit signature enhancements. SEP's IPS Audit Signatures do not block traffic, but empower SEP administrators to learn which endpoints in their network are connecting to websites using this vulnerability. The administrators can take action as they see fit (creating firewall rules, application and device Control policies, and so on).
Update – March 10, 2015:
Apple has issued a patch for iOS (8.2) and a patch for OS X (2015-002) that fixes the FREAK vulnerability. Users are advised to update and apply these patches to their Apple devices.