
Since the beginning of 2014, a single individual conducted a vast spam operation on Twitter for over a year by using nearly 750,000 fake Twitter accounts. These accounts were part of an elaborate scheme to peddle a type of diet pill known as Green Coffee Bean Extract. Through the use of affiliate programs, the spam operator would earn a commission for each successful referral.

Figure 1. Fake Women’s Lifestyle website promoting Green Coffee Bean Extract
To convince users that the pills are legitimate, the scammer used a series of brand and celebrity impersonation accounts on Twitter. The scammer also leveraged fake Twitter accounts to drive real Twitter users to these impersonation accounts. Despite creating nearly half a million accounts and using creative ways to maintain persistence on Twitter, the scammer was careless and left a few clues about his identity throughout the course of the campaign.
Symantec has kept Twitter informed of this operation and shared our findings in advance of publication. We have also shared our findings with Bitly, Google, and GoDaddy, including all known short URLs and fully qualified domain names used in the operation.
For an in-depth look at the mechanics of this spam operation, please check out our whitepaper: Uncovering a persistent diet spam operation on Twitter
Impersonating brands and celebrities
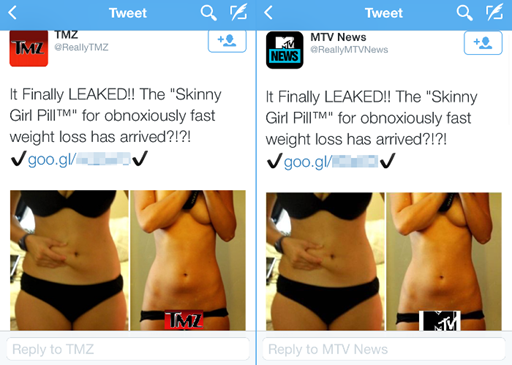
Figure 2. Impersonation accounts for TMZ and MTV News
This spam operation leveraged a number of brands, from major news organizations like CNN and ABC to entertainment-focused outlets like TMZ, MTV News, and E! Online. Reality TV stars like Jersey Shore’s Nicole ‘Snooki’ LaValle and Geordie Shore’s Vicky Pattinson were also impersonated because of their notable weight loss efforts.
Account types: Eggs, Parrots, and Mockingbirds
There are three types of accounts involved in this elaborate scam. We have classified these as Eggs, Parrots, and Mockingbirds.
- Egg accounts resemble new Twitter users. The name refers to the default avatar associated with Twitter accounts that have not selected a profile photo.
- Parrot accounts use stolen photographs of real women and “parrot” text and image-based tweets posted by real users.
- Mockingbird accounts are celebrity and brand impersonation accounts.
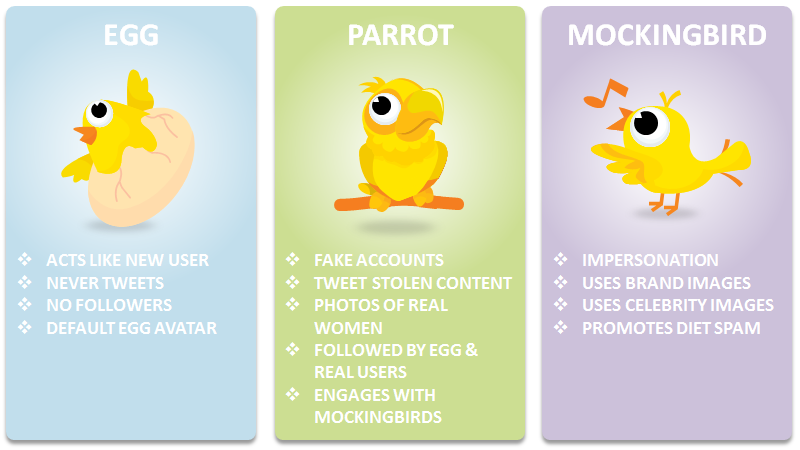
Figure 3. Account types used in this operation
How this spam operation works
The main account types, Mockingbirds and Parrots, are used to spread the scam to as wide a pool of Twitter users as possible.
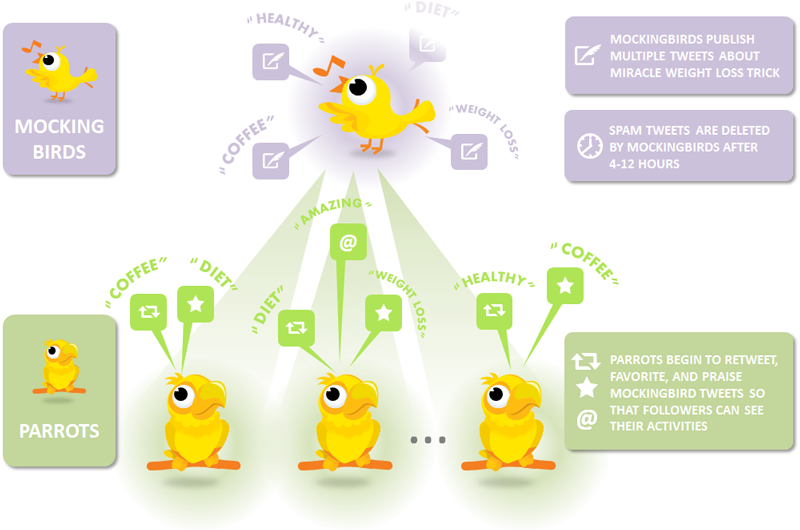
Figure 4. Mechanics of the spam operation
- The Mockingbird accounts publish one-to-four tweets in succession containing text about the miracle weight loss trick along with a before-and-after image and a shortened URL
- Within a few minutes, the Parrot accounts are instructed to retweet and favorite these tweets to publicize them to their followers
- The Parrot accounts tweet replies back to the Mockingbird accounts, praising these miracle diets
- The spam tweets remain live for anywhere between 4 to 12 hours
- The Mockingbird accounts then delete the miracle weight loss tweets

Figure 5. Example of Parrot accounts engaging with a spam tweet from a Mockingbird account
Recovering from account suspension
Each account serves a specific purpose in the spam operation. However, we found that once Twitter discovers and suspends these Parrot or Mockingbird accounts, the operator will replenish his resources by converting Eggs to Parrots and Parrots to Mockingbirds.
Distribution of accounts
Throughout our research, we regularly queried the Twitter API to get a bigger picture of this spam operation. Our findings showed that the spam operator has had nearly 750,000 accounts that we know of at his disposal.
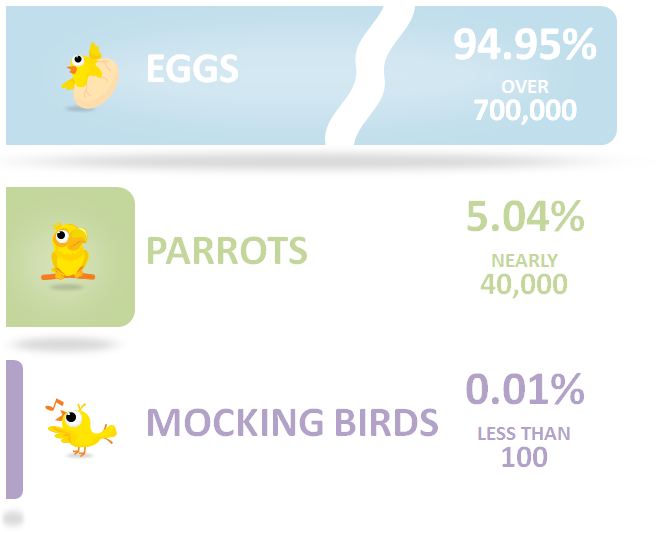
Figure 6. The account types and number of them in the scheme
The bulk of these accounts are Eggs. This makes sense for one primary reason: many Twitter users who join the service never publish a tweet. By using these Egg accounts to only follow other users, it makes them less of a target than Parrot and Mockingbird accounts for suspension.
Identifying the spam operator
Despite using clever tactics to maintain persistence, the spam operator left clues about his identity in domain registrations, short URL accounts, and even made the mistake of converting one of his Parrot accounts into a personal account for himself. He also used some of the Parrot accounts to retweet and favorite personal tweets.
Cashing in on the demand for dietary supplements
Over the years, we have seen a number of spam campaigns circulating through various social networking applications and services. Whether it is on Instagram, Snapchat, Pinterest, or Tumblr, spammers are trying to capitalize on the weight loss dietary supplement industry, which nets US$2 billion annually. We expect these types of spam operations to continue as a result.
For Twitter users, some key takeaways from this spam operation:
- Look for the blue verified badge. Twitter continues to face the problem of impersonation accounts of brands and celebrities. This spam operation convinced enough users that these impersonation accounts were legitimate. Twitter users should always check to see if the brand or celebrity has been verified before following. The blue verified badge denotes that Twitter has verified the authenticity of an account.
- Be skeptical of new followers. If a random person follows you, do not automatically follow them back. Look at their tweets. Are they retweeting content that looks spam? If so, then they are likely a bot.
- Numbers can lie. Even if these random followers have tens of thousands of followers, those numbers can easily be faked. Do not base your decision to follow them back because of how many people follow them.
- There is no such thing as a miracle diet. At the end of the day, weight loss requires more than just a dietary supplement. Exercise and healthier eating is necessary in order to see real results when it comes to weight loss.
Learn more about this spam operation in our whitepaper: Uncovering a persistent diet spam operation on Twitter
