Advanced Authentication Mainframe (AAM) with ACF2
My first blog about Demystifying ACF2 provided an overview of ACF2. Moving forward, I am going to select different aspects of ACF2 based on the customer interest. In this blog, I focus on Advanced Authentication Mainframe (AAM). AAM takes security to the next level by verifying the identity of users who seek access to z/OS to prevent data breaches and to address compliance requirements.
ACF2 version 16.0 supports AAM. It is available to all ACF2 licensed customers at no additional cost. The following Multi Factor Authentication (MFA) capabilities are available for z/OS application logon processing for MFASTC started task as shown in Figure 1 using:
- RSA SecurID credentials (instead of ACF2 password/password passphrase)
- Common access card (CAC) or personal identity verification (PIV) smart card followed by an ACF2 password/password passphrase
- RADIUS credentials (instead of ACF2 password/password passphrase)
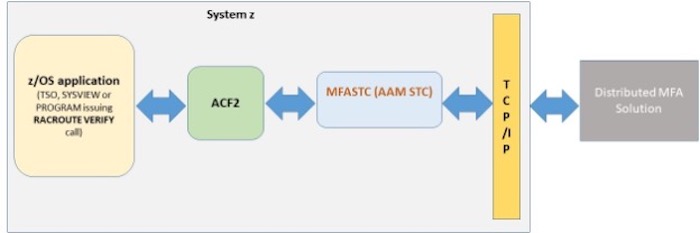 Figure 1: AAM Logon Processing
Figure 1: AAM Logon Processing
Apply the latest AAM maintenance from mainframe support portal page and try out the functionality!
The log4j vulnerability made big news in the security world lately, so let’s discuss it for AAM:
- Log4j 2.x vulnerability: AAM is not affected by the more serious CVE 2021-44228 vulnerability applicable to log4j 2.x.
- Log4j 1.x vulnerability: AAM is affected by the less severe Log4j 1.2 CVE-2021-4104 vulnerability when specifically configured to use JMSAppender, which is not the default.
The PTF LU04132 contains remediation for the less severe log4j CVE-2021-4104 Vulnerability. It discusses the need to remove a previously bundled Log4j 1.2.17 in mfav1.jar. This PTF also includes support for using the RSA SecurID Authentication REST API and RSA SecurID Authentication Replica Servers.
If you are using the CAAAMRSA factor[1], we recommend that you enable RSA SecurID Authentication API (REST), which we delivered in PTF LU04132.
If you can’t immediately enable REST API support, you can continue to use the RSA SecurID Authentication API for C and Java (SDK) until you are ready to enable it. However, you must copy the RSA provided log4j-1.2.12rsa-1.jar to the RSA_HOME directory where authapi.jar and cryptoj.jar are located.
Running into any issues? The Broadcom support team is happy to assist. Here are some pointers to collect the debug data for quick analysis of issues:
- Obtain the MFA started task log showing the error message
- Turn on AAM tracing by updating *logback.xml* file in AAM directory for parameters towards the bottom and set it to <root level=”TRACE”>. xml is an ASCII file and must be updated in ASCII format. Recreate the problem with tracing turned on.
- Obtain the Daily log residing in USS directory called LOGS under: /nonshare/Prog_Products/CA_MAA
FTP the log and trace data to Broadcom support site. We will help you figure out any configuration errors in your environment. We can’t wait for you to try out this functionality and for you to let us know what you think!
[1] To determine if you are using CAAAMRSA factor, there will be an RSA Agent running on the z/OS platform and an RSA Authentication Manager where RSA credentials are validated. In ACF2, logonids that use RSA authentication must have access to a resource with $KEY(RSA). The resource rule class name is CASECMFA, and the three-character type code, by default, is CAS.