Works like a charm for me...
here...hope this helps...
Sorry if I really went basic but it worked for me without any issue so figured I would walk through very detailed steps so maybe if it helps others too...
Create a new policy and choose Rule
Product name: Google Chrome
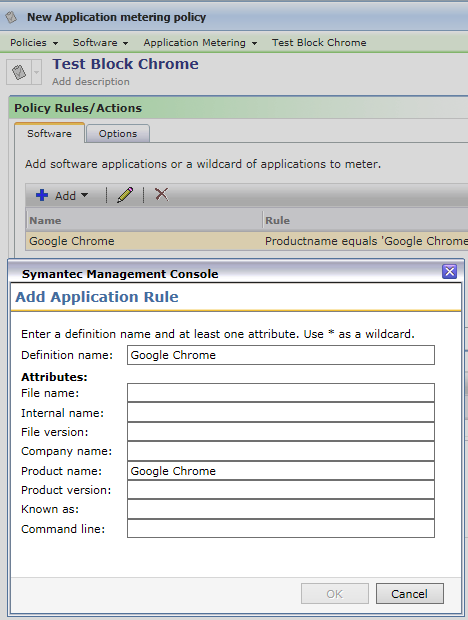
1. verify policy shows correct information
2. verify your target test machine shows in list
3. verify policy is enabled

Test machine
- Click update
- verify requested and changed update (as this will represent new policy came down)
- Verify you do have the app metering agent installed

should be good to go and block.... I also added a message to the users... back on the options tab in the policy

also you can go into the altiris queue directory and find your metering information that goes to Altiris.
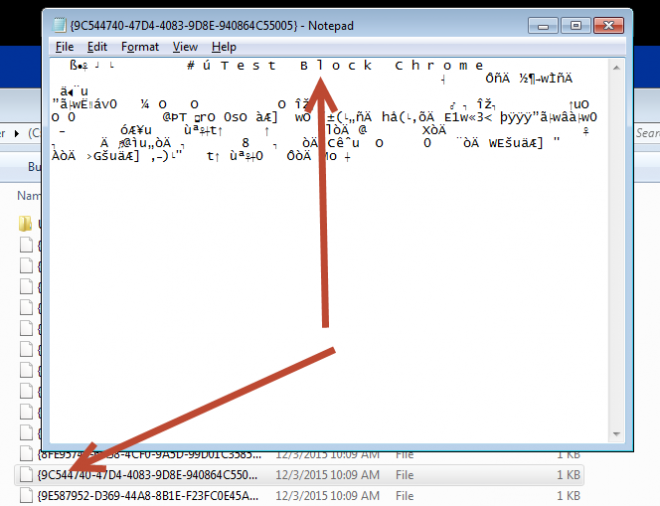
Goto your policy, right click and choose properties
Take the guid number
go into the altiris agent\queue directory and look for the guid number
open with a text editor
Policy is there and good to go....
should be working