Dear friends,
I spent many hours trying to get loginServiceManaged to work and I'm more and more confused
What I tried:
1. using pdm_pki I generated the DEFAULT.p12 certificate for the DEFAULT WS Policy
2. I copied the DEFAULT.p12 cert to the axis folder
3. I followed the step by step example in ..\sdk\websvc\perl\test1_pki\opensslSample.sh for DEFAULT policy (with password DEFAULT):
openssl pkcs12 -info -in DEFAULT.p12 -out file.pem -passout pass:dummy
openssl x509 -in file.pem -pubkey -noout > DEFAULT.pub
openssl pkcs12 -in DEFAULT.p12 -nodes -nocerts -out DEFAULT.priv
echo -n "DEFAULT" | openssl dgst -d -sign DEFAULT.priv -sha1 > file.bin
echo -n "DEFAULT" | openssl dgst -verify DEFAULT.pub -signature file.bin -sha1
openssl base64 -e -in file.bin -out file.b64
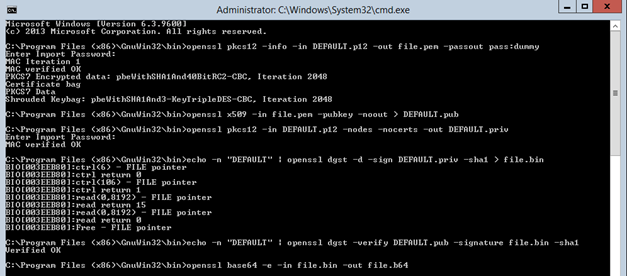
4. The results of all the commands seem to be OK
5. The final encrypted_policy string also seems to be nice
fzK745Qa60GYN65qXhJB1GlIbqe5PXKWemCeemJTcViM4XYYnNbNOEJOX0fdgb8u
LQN0lSgumQEwmpsBj5aPoKrRpGM+gc1uPn9wUEfaDgzqQLgrjT/lh1f7RUW/Xx5o
EP1jJgTAbSeoL0o/mfE4aBO1ZXfMIrXjer4mwMDsHIj0H46sEw3A9+9YiOJFv//Y
ItPN+eYliCgg1LjcUFi0twPb3Nx2BrmEPtvuYA7l0Bkrs52l2TJD3/lMnwx40V0R
R3y2uZeEzum3GlZErCxEzehj9v3b5z2Tqp0L+W+kVCXur+Lm5GXJCSQRkQO0yhPr
y+36eQ4yeoVJyEoJC8Q6Ew==
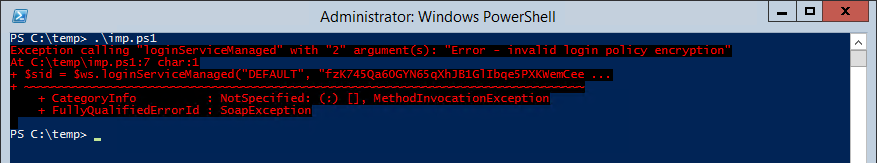
But it simply doesn't work in my powershell script
$wsurl = "http://itasm:8181/axis/services/USD_R11_WebService?wsdl"
$ws=New-WebServiceProxy -uri $wsurl
$sid = $ws.loginServiceManaged("DEFAULT", "fzK745Qa60GYN65qXhJB1GlIbqe5PXKWemCeemJTcViM4XYYnNbNOEJOX0fdgb8uLQN0lSgumQEwmpsBj5aPoKrRpGM+gc1uPn9wUEfaDgzqQLgrjT/lh1f7RUW/Xx5oEP1jJgTAbSeoL0o/mfE4aBO1ZXfMIrXjer4mwMDsHIj0H46sEw3A9+9YiOJFv//YItPN+eYliCgg1LjcUFi0twPb3Nx2BrmEPtvuYA7l0Bkrs52l2TJD3/lMnwx40V0RR3y2uZeEzum3GlZErCxEzehj9v3b5z2Tqp0L+W+kVCXur+Lm5GXJCSQRkQO0yhPry+36eQ4yeoVJyEoJC8Q6Ew==")
$sid
#$sid2 = $ws.impersonate($sid,"jarnold")
#$sid2
$ws.logout($sid)
The error is "Error - invalid login policy encryption"
Also the DEFAULT policy seems to be correctly defined..

Any ideas?
Thank you,
Jakub