Team,
Instead of using the tools of IM Config Xpress, imagine using this process to version control your CX source code from current production environment.
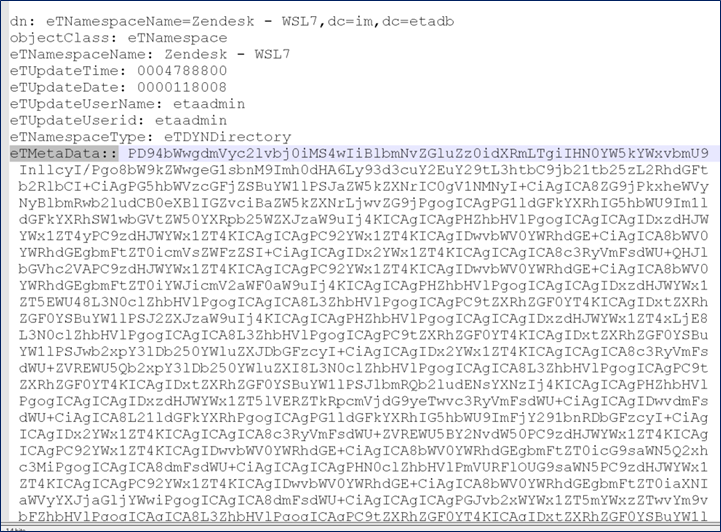
Background: When CX UI is used to push/store its configuration to the IM Provisioning Server, this XML information is stored on the Endpoint Type for this connector as an ldap attribute labeled eTMetaData. Due to the size and UTF-8 characters, this data when exported, is shown as base64 encoded, e.g. double colon (after the ldap attribute).
To view this data, we can use the Linux/Unix command line tool of base64 with the -d switch to decode.
Example below for namespace "Zendesk". See the base64 data in eTMetaData.
To view this data, combine a ldapseach/dxsearch query, use perl to force a no-wrap of the ldif export; then use awk/grep to streamline the data for using base64 to decode the data.
Example:
dxsearch -LLL -h `hostname` -p 20396 -c -x -D "eTDSAContainerName=DSAs,eTNamespaceName=CommonObjects,dc=etadb" -w "Password01" -b "eTNamespaceName=Zendesk - WSL7,dc=im,dc=etadb" eTMetaData | perl -p00e 's/\r?\n //g' | awk '{print $2}' | grep -v "eTNamespaceName=Zendesk" | grep -v "eTDYNPolicyContainerName=DYN" | grep -v "eTDYNPolicyName=DefaultPolicy,eTDYNPolicyContainerName=DYN" | base64 -d
Output:
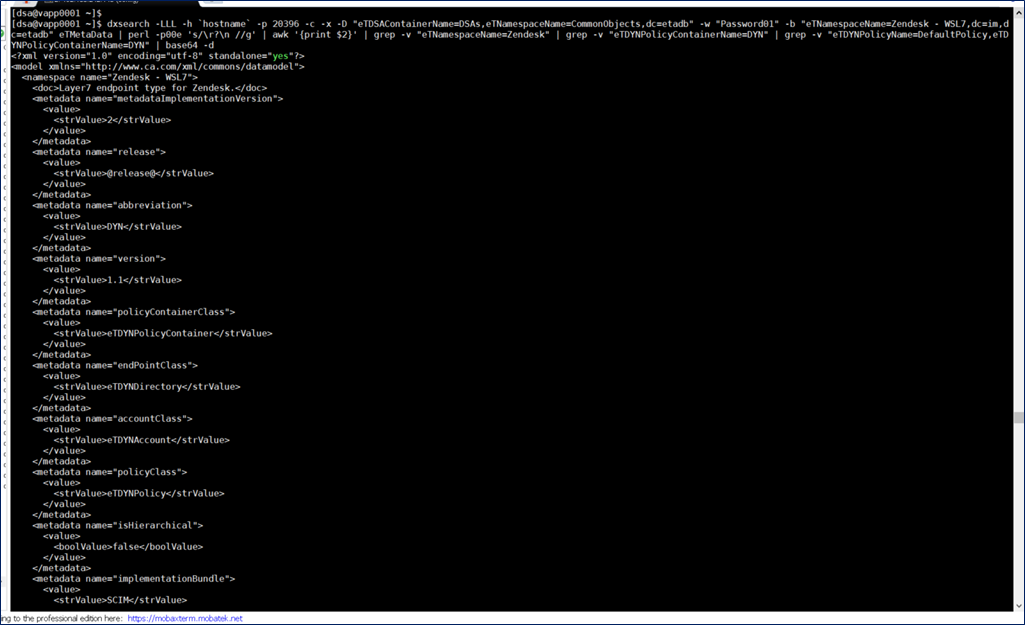
The above file may be re-directed to a new output file with a time-date-stamp.
Hint:
When using the above command, run it first in parts, to identify which strings to grep/remove prior to using base64 decode.