Hi Lav,
Since you are working with CA Support, they probably already provided you with a solution. Otherwise, two alternatives come to my mind off the top of my head to achieve your requirement:
1) you can write a java plugin in CA Identity Portal that queries the Role attributes and then you can use this information in the form handlers. Access request execution path is based on a form after all. Please search java plugin functionality in the Identity Suite documentation on docops.ca.com
2) Do you have CA Identity Governance? In CA Identity Governance you have a possibility to define business policies (BPRs) based on counters, i.e. User Counters of Role and you can define the maximum number of users that could have access to this role. Then you can use Identity Governance BPR rules as risks in Identity Portal or configure Smart provisioning in Identity Manager. Please see below my screens as an example:
Identity Governance User Counters of Role BPR Screen:
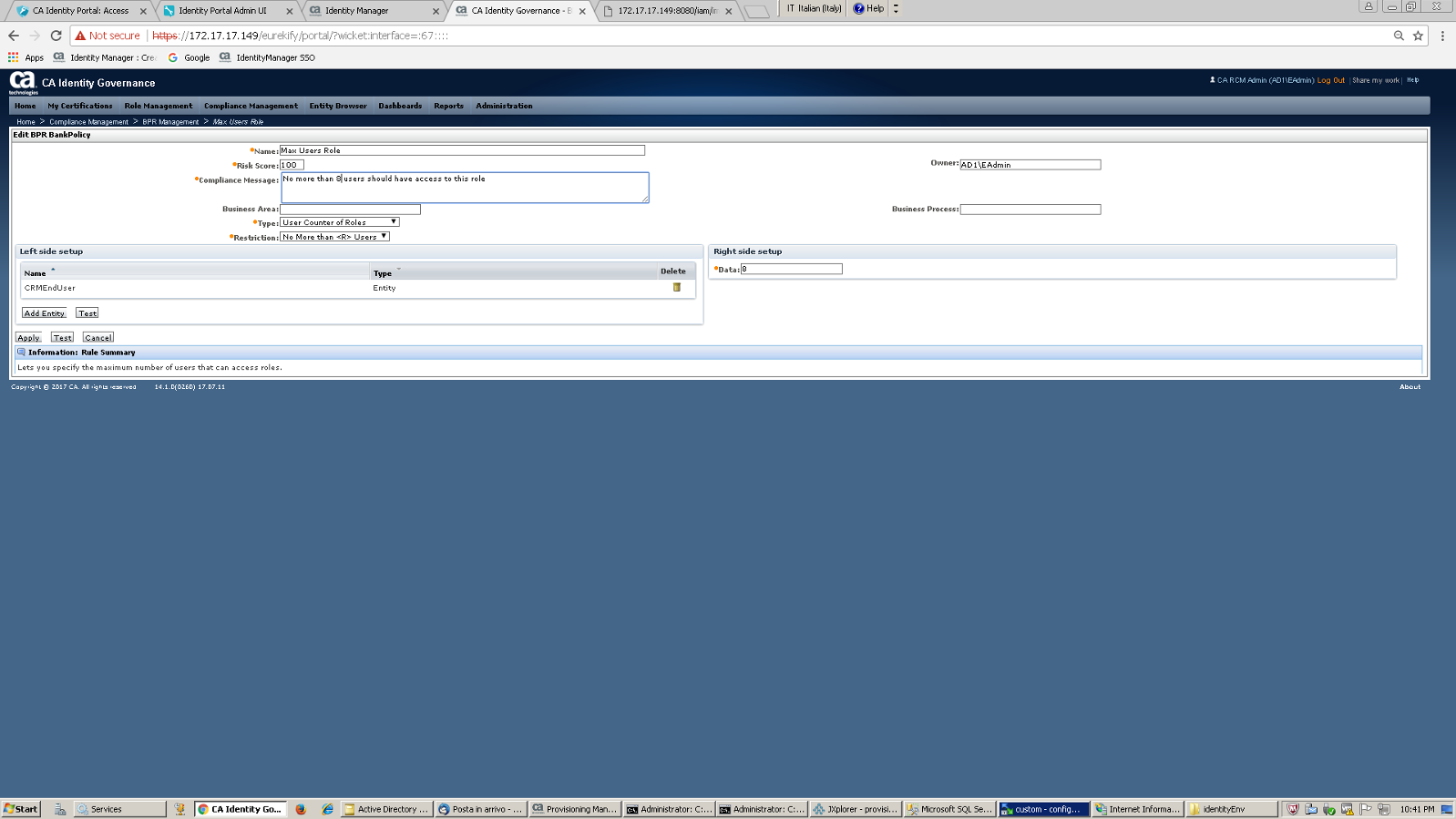
I have already exceeded max of 8 users for the CRMEndUser role, so this BPR is already violated.
Here's the message the user receives when checking out CRMEndUser role from Identity Portal as access request WITHOUT defining risk in Identity Portal (this is because smart provisioning is configured in Identity Manager which checks for IG BPR violations). As you can see the BPR compliance message is displayed by CA Identity Manager to the end user.
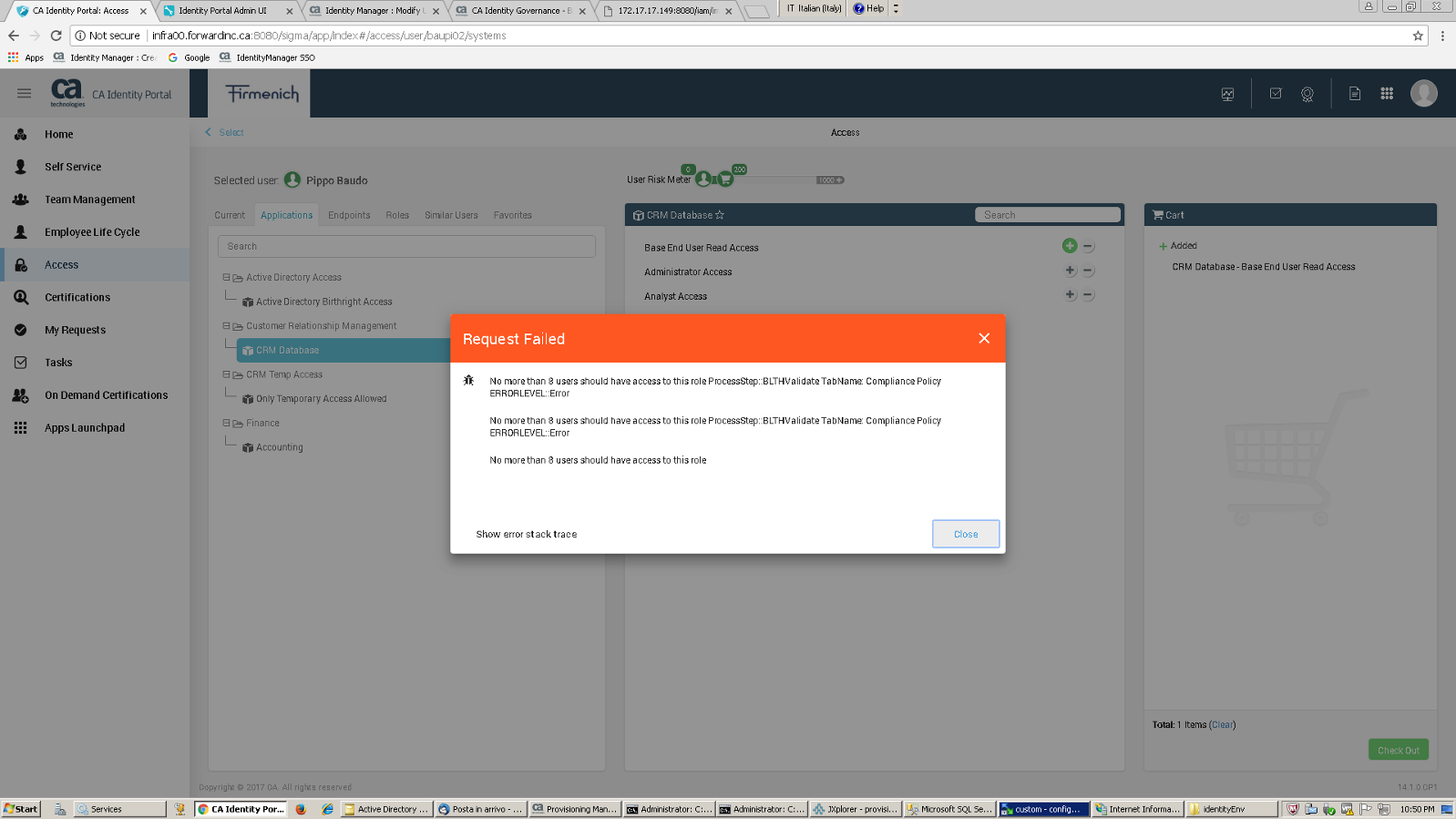
You can also use Identity Governance risks in Identity Portal and it would likely look much prettier to the end user. If Identity Governance violations are checked in Portal, they would increase the risk score of the cart and the user would not be allowed to check out access based on blocking risks and the user will receive a more user friendly message.
I can't share the Identity Portal risks display screens during the access requests at the moment but I may be able to do so in the future should you be interested.
KR
Russi