Team,
When you need to identify an SSL issue or authentication issue, sometime it is useful to see the HTTP request as it is submitted. If you can disable SSL, and the transaction works, then you may wish to use this process to continue your debugging steps.
I was previously using Wireshark notes about extracting the server key or CA key to decrypt traffic. However, this is difficult for some customer environments. Especially for production environments.
I found Jim Shaver notes, using an Environmental variable to capture the session keys, as a very easy process to implement a process to de-crypt HTTPS traffic .
https://jimshaver.net/2015/02/11/decrypting-tls-browser-traffic-with-wireshark-the-easy-way/

No need to update RSA Key list with CA or Server private key cert.
Example of session keys captured:

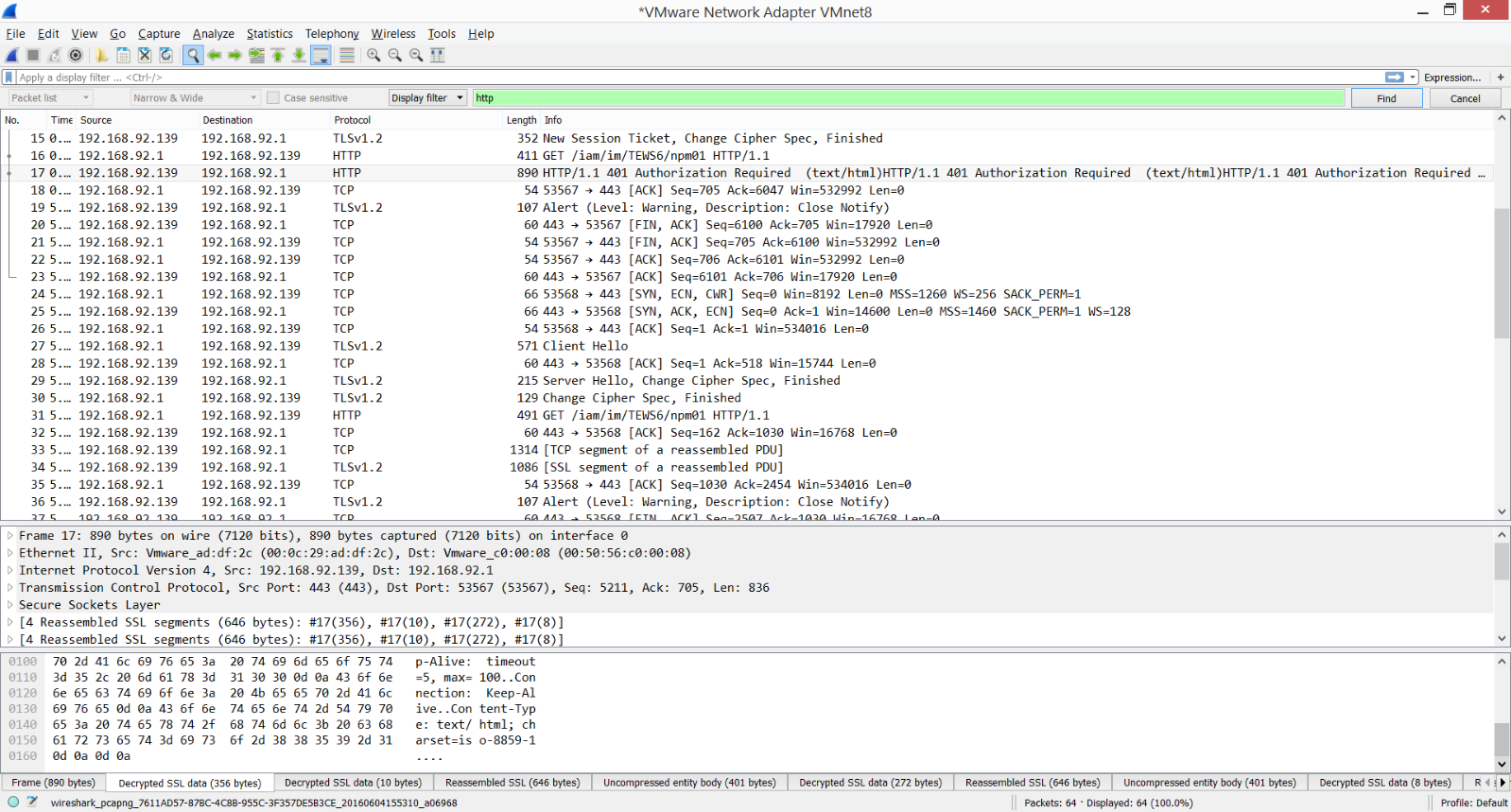
Within Wireshark, there will be a TAB, at the bottom screen, for any SSL traffic, called "Decrypted SSL Data"
Let me know if you find this of use.
This can be implemented on any workstation (win/linux); without the need of the CA or server private key.
Cheers,
A.