Hi all,
The SSL process continues.
Attempting to complete this process:
How to replace a self signed SSL certificate with a 3rd party signed cert
I have no luck using a .p7b in the keystore. So I have been using the .CRT that was created along with a .KEY file.
I created the keystore file doing the following command:
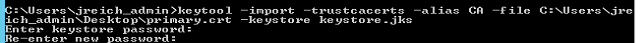
This resulted in a keystore.jks file. This file was moved to the C2O/.CONFIG location.
Edited the OasisConfig file to adjust the following three lines...
#Defines the path of the keystore that is used for signing jars.
itpam.web.keystorepath=C:/Program Files/CA/PAM/server/c2o/.config/keystore
#Defines the password of the keystore that is used for signing jars.
itpam.web.keystore.password=**********
#Defines the alias name of the certificate in the keystore that is used for signing jars.
itpam.web.keystorealias=CA
Password has been removed. But the password being used was the direct password as a test. Not one that was encrypted for use in the file by the system.
I attempted to use C:/Program Files/CA/PAM/server/c2o/.config/keystore and
C:/Program Files/CA/PAM/server/c2o/.config/keystore.jks
When starting up PAM it was launch the first JAVA process and begin the boot-up process. It will never boot fully. It will eventually switch the service back to STOPPED.