Hi all
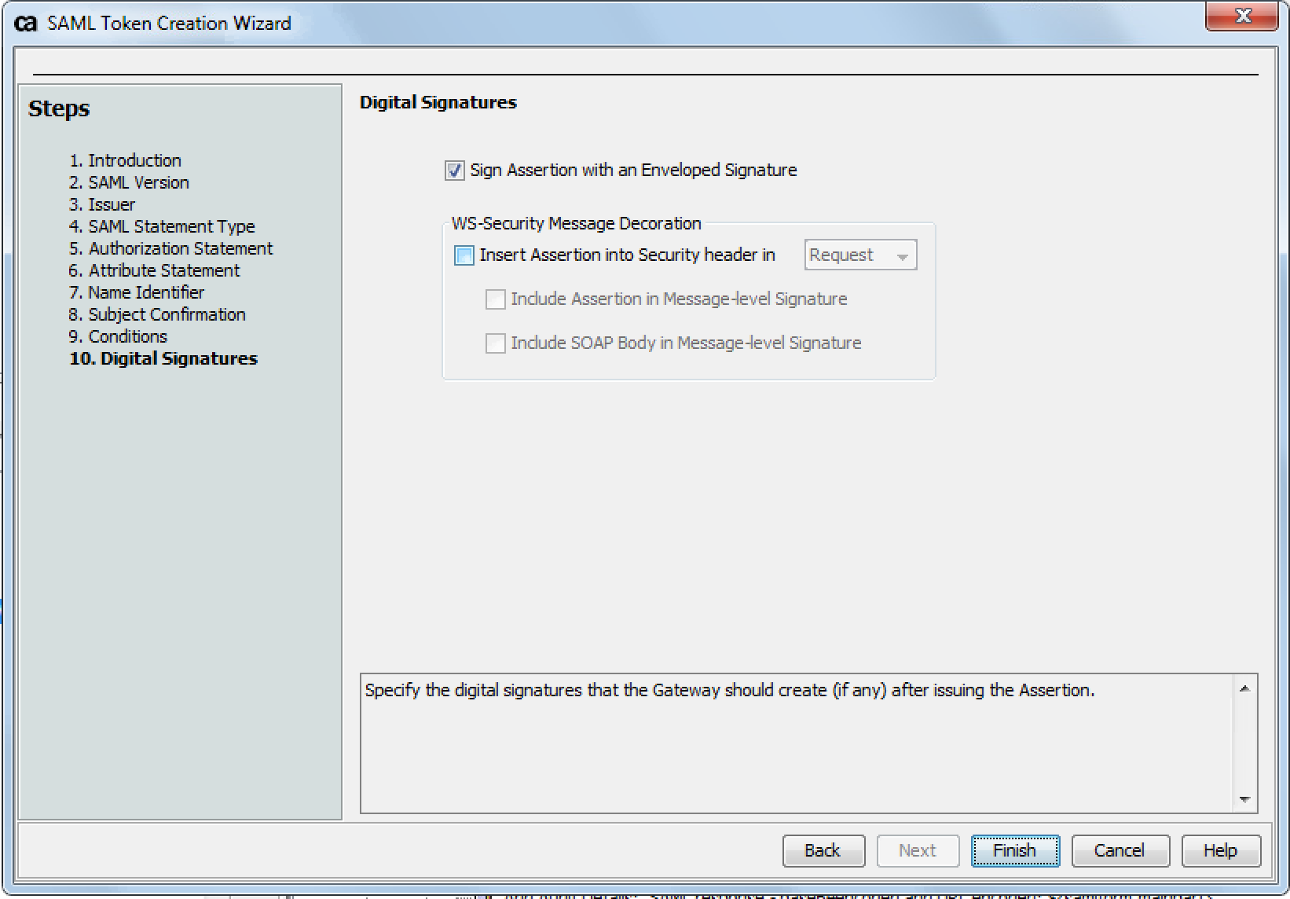
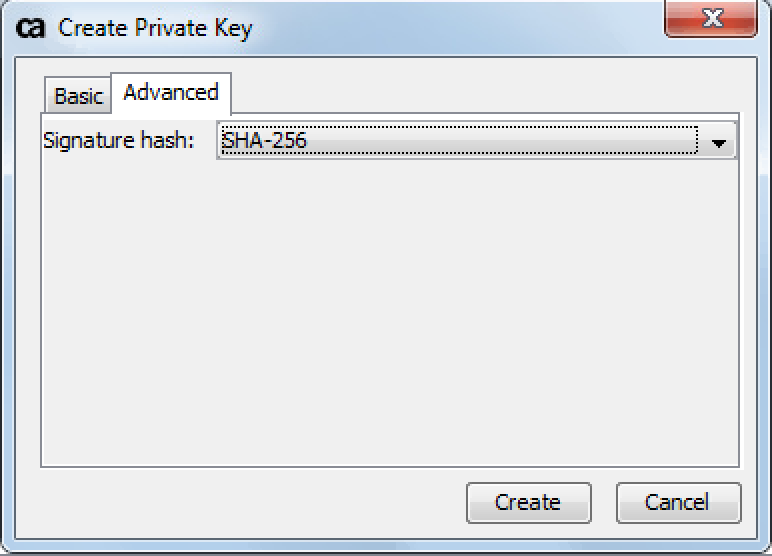
We're trying to sign a SAML token using the SHA 256 algorithm. We're using the "Create SAML Token" assertion to generate the SAML token. On step 10 we enable the checkbox "Sign Assertion with an Enveloped Signature" (see screenshot below). On the assertion we selected a private key which was generated using the SHA-256 algorithm (see second screenshot below).
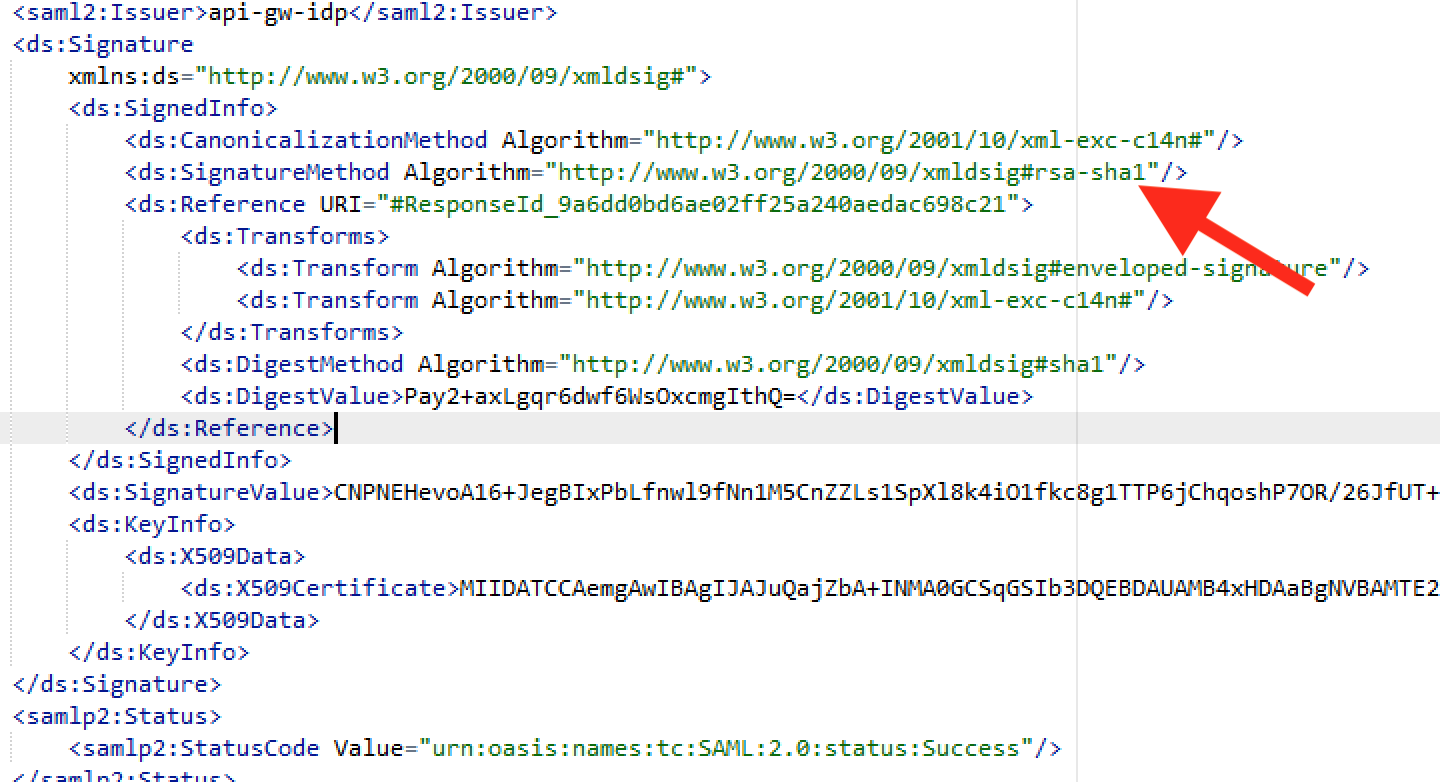
However when looking at the generated SAML assertion xml, the used signature algorithm is SHA-1 (see last screenshot below). We see the same behaviour when signing using the "Build SAML Protocol Response" assertion.
Does anyone know how this should be configured to make sure the SHA_256 algorithm is used when signing?
Tested this on API Gateway version 9.1.01.
Thanks
Samuel