Summary:
In this guide we will see how to configure CA SSO to overcome the challenges associated with Web 2.0 websites.
Web 2.0 websites allows users to do more than just retrieve static content from the server.
It does this by running script engine in the context of the browser.
Examples of Web 2.0 technologies :
- Ajax
- Silverlight
- Adobe Flex
- Java Web Start
Challenges with CA SSO for the Web 2.0 support :
- It expects response in the certain format. It doesn't understand CA SSO challenges and authentication redirects.
- The regular polling can prevent idle timeout expiration.
- It may support HTTP methods other than the usual Get/POST
Environment:
- Policy Server : R12.52+
- Web Server : Apache
- Web Server OS : Linux
- Web Agent : 12.51 CR3
Instructions (summary):
1) Configure any of the following ACO parameter (as applicable) to identify Web 2.0 resources and as such prevent their access from creating/updating session cookies.
- OverlookSessionForMethods
- OverlookSessionForUrls
- OverlookSessionAsPattern
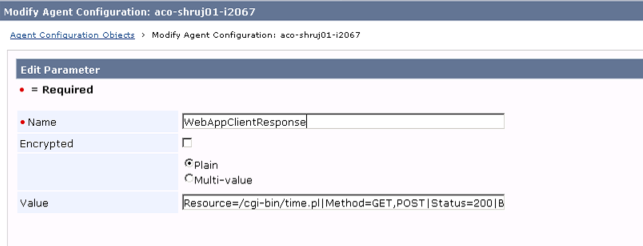
2) Configure WebAppClientResponse ACO parameter to identify Web 2.0 resources and configure customized response to integrate CA Single Sign-On generated behavior (e.g. challenge/idle time out /maximum time out etc) , with the functionality of the web application client.
3) Configure the web application to handle a custom response returned by CA SSO.
Instructions (Detailed):
Configure Web Server
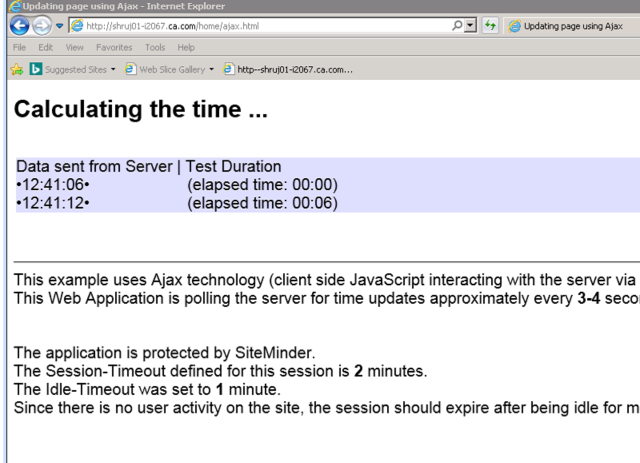
To demonstrate CA SSO support to Web 2.0 application , we will deploy the sample Ajax application (attached) on our web server and make necessary changes to protect it.
- Deploy the application as below (either jQuery or XmlHttpRequest sample) :
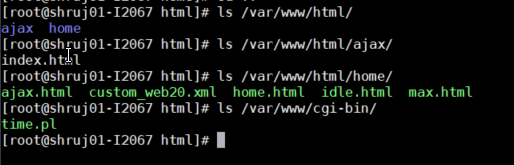
- Configure /var/www/cgi-bin/ as ScriptAlias (refer to attached httpd.conf)
- Configure /var/www/html as DocumentRoot (refer to attached httpd.conf)
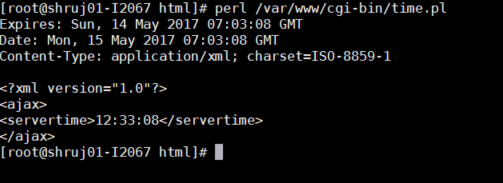
- Test the sample perl script (time.pl) and ensure it's working
- Access the Ajax web site directly and ensure it's workinghttp://<fqdn>/home/ajax.html
Configure CA SSO Policy Server
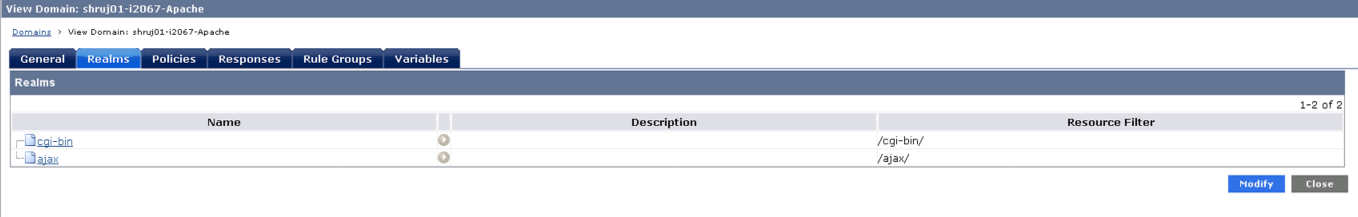
- Protect resources /cgi-bin/ & /ajax/. Leave /home/ unprotected.
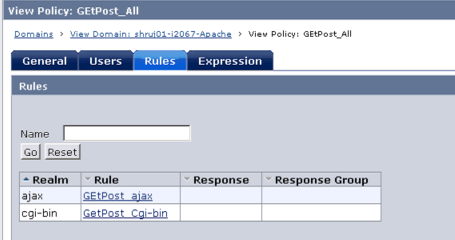
- Configure OverlookSessionForUrls ACO parameter to identify /cgi-bin/time.pl as Ajax resource. This will prevent Session cookie creation/update while accessing this resource, effectively allowing the user session to idle time out.
- Configure WebAppClientResponse ACO parameter to identify Ajax resources and configure customized response
Resource=/cgi-bin/time.pl|Method=GET,POST|Status=200|Body=/var/www/html/home/custom_web20.xml|Content-Type=application/xml|Charset=us-ascii
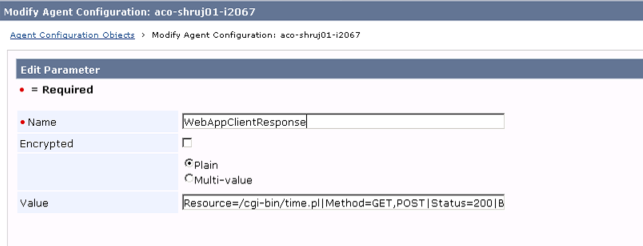
Note : Ensure that the Body points the absolute location of the customized response XML file on the web server. This custom response file can be customized to include any other additional details, but at minimum it must include: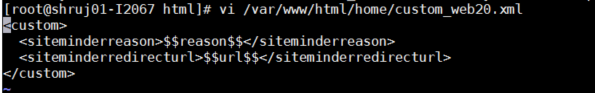
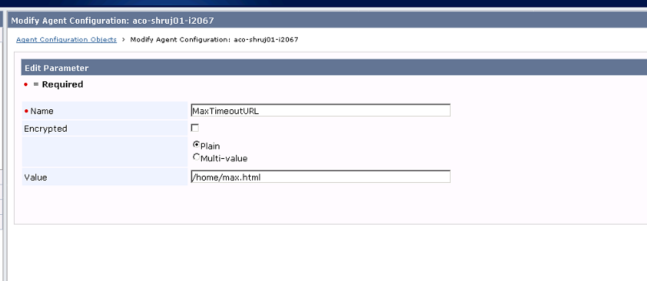
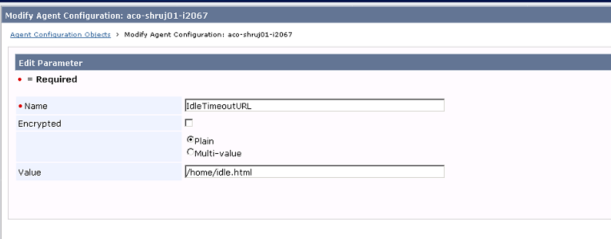
- Configure MaxTimeOutURL & IdleTimeoutURL ACO parameters
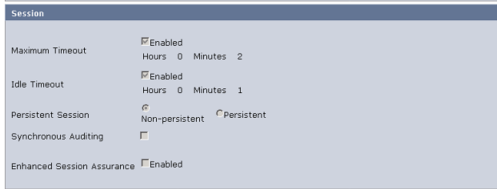
- Configure Session Idle/Max Timeout as required.For this demonstration we will keep it as following :IdleTimeout = 1 Minute, MaximumTimeout =2 Minutes
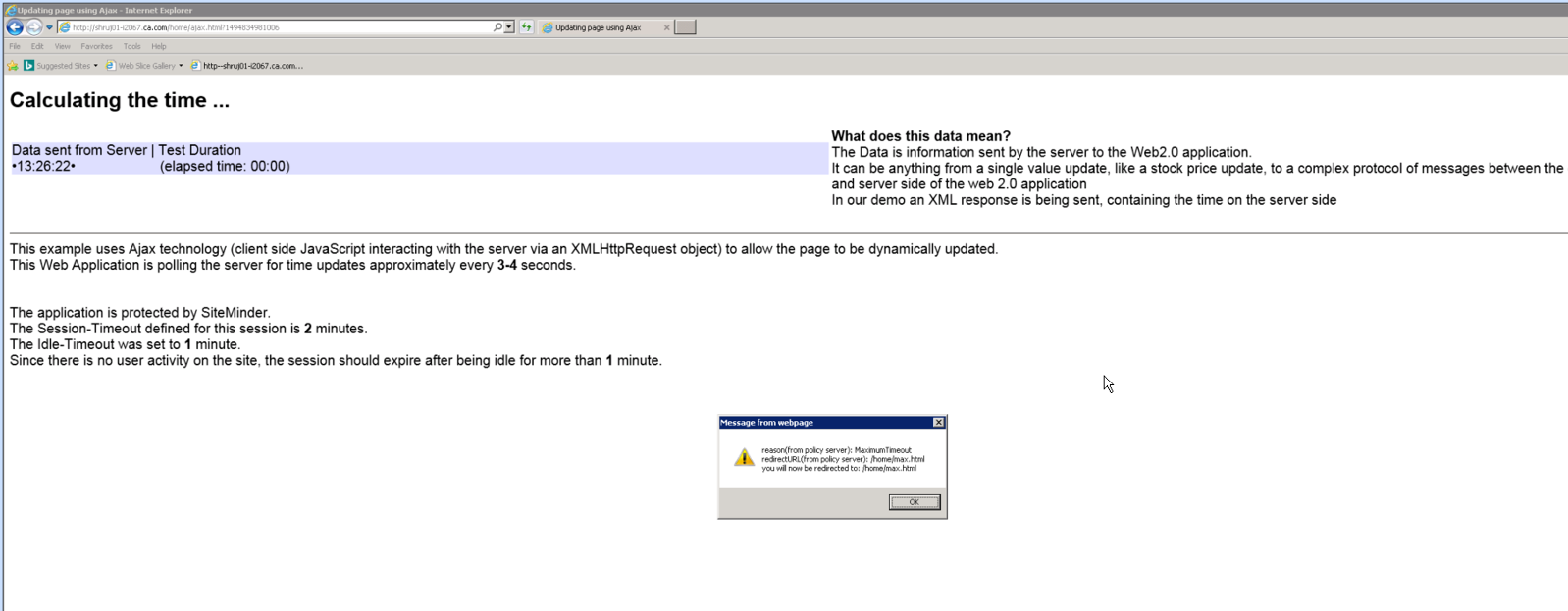
- Configure Web 2.0 application to handle all CA SSO custom responses. For e.g as you can see below, in the sample application (ajax.html) , if CA SSO returns the reason as MaximumTimeout or IdleTimeout, it reads the redirectURL returned and redirects to it if it's not empty otherwise , it redirects to the home page. In case of Challenge , as CA SSO doesn't return any redirectURL , it then redirects directly to the home page.
else if ((reason == "MaximumTimeout") || (reason == "IdleTimeout")) {
var alertMessage;
alertMessage = "reason(from policy server): " + reason;
alertMessage += "\nredirectURL(from policy server): ";
alertMessage += redirectURL;
if (redirectURL == "") {
redirectURL = "/home/home.html";
}
alertMessage += "\nyou will now be redirected to: ";
alertMessage += redirectURL;
alert(alertMessage);
redirectURL += "?reason=" + reason;
document.location = redirectURL;
return;
}
else if (reason == "Challenge")
{
redirectURL = "/home/home.html";
document.location = redirectURL;
return;
}
}
Testing:
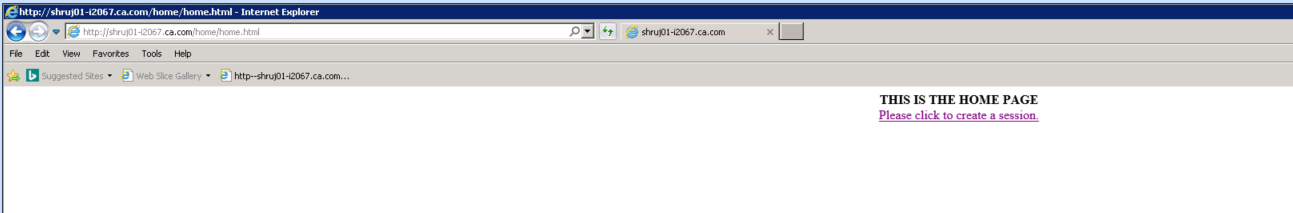
Use Case 1 : Challenge
In this use case we will access the ajax resource which is protected by CA SSO but without having SMSESSION already in the browser.
So access : http://<FQDN>/home/ajax.html
As you can see, as the browser currently doesn't contain the SMSESSION, it receives the customized response from Web Agent with :
- Reason: Challenge
- RedirectUrl : <empty>
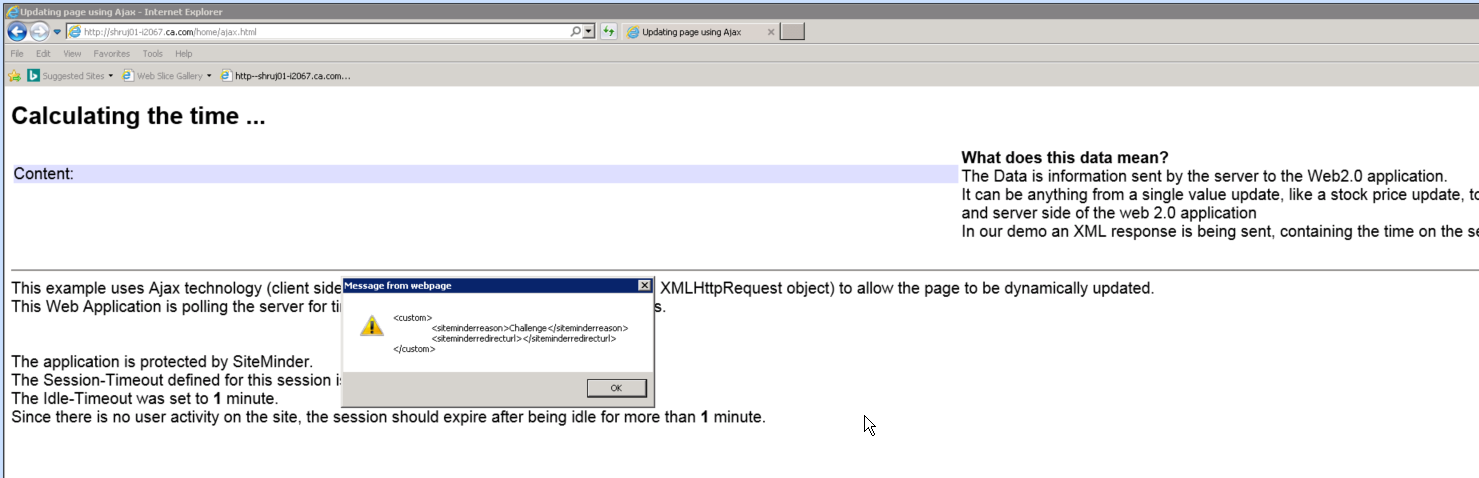
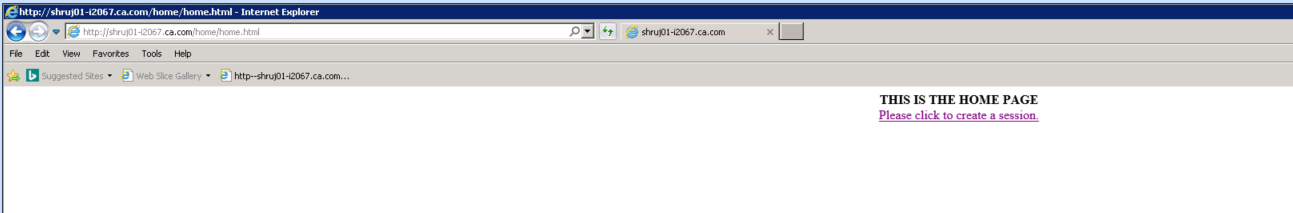
Now, as the Ajax application is configured to redirect to home page under this condition, it redirects accordingly.
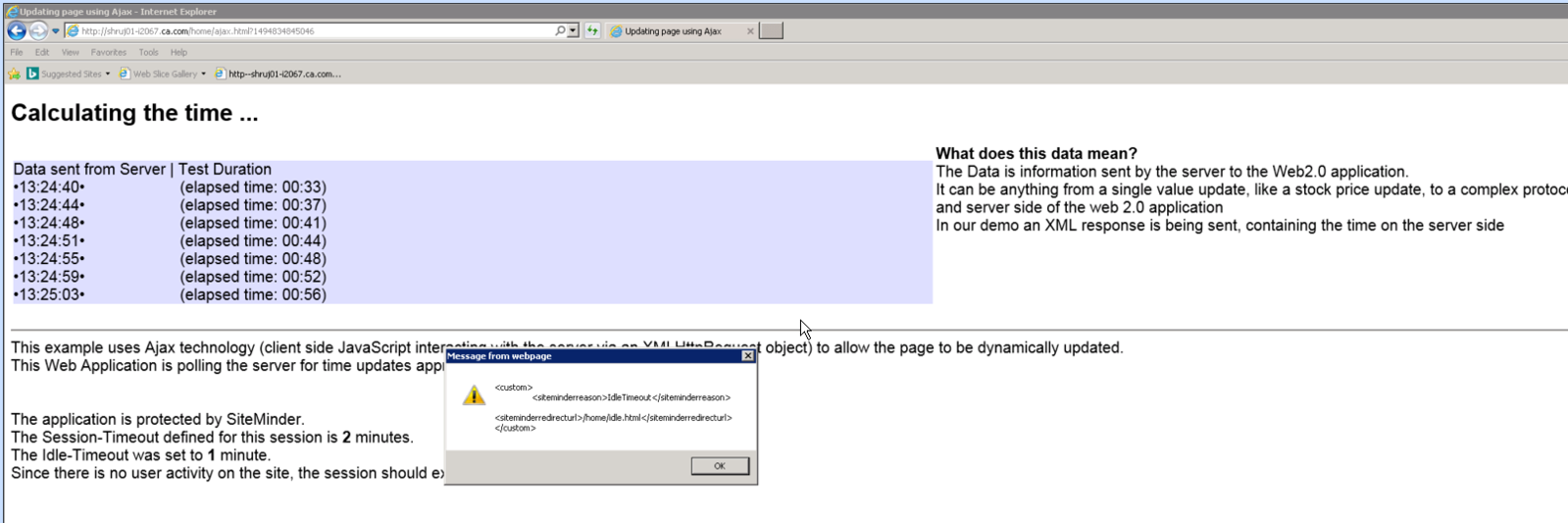
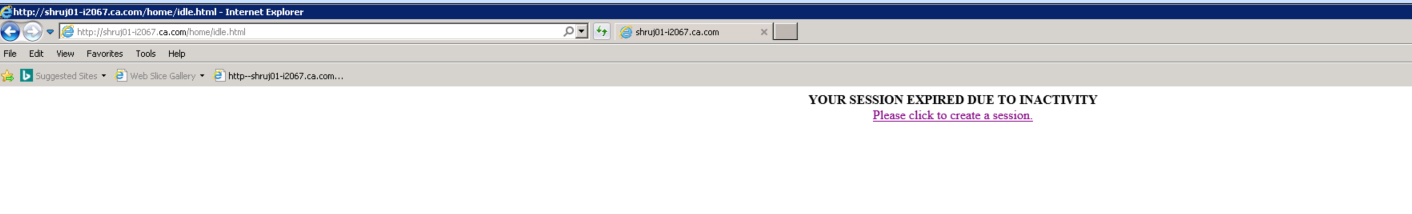
Use Case 2 : Idle Timeout
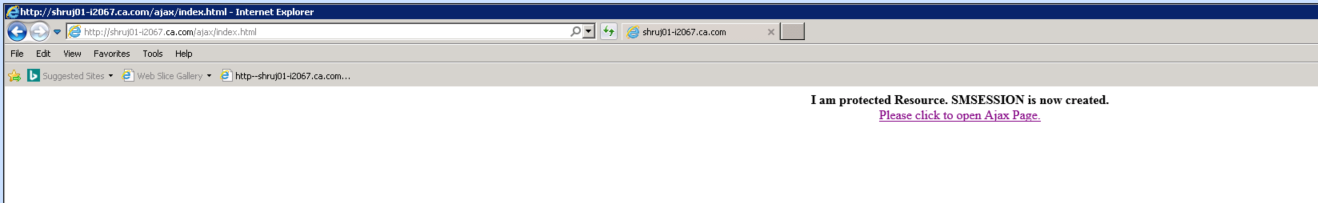
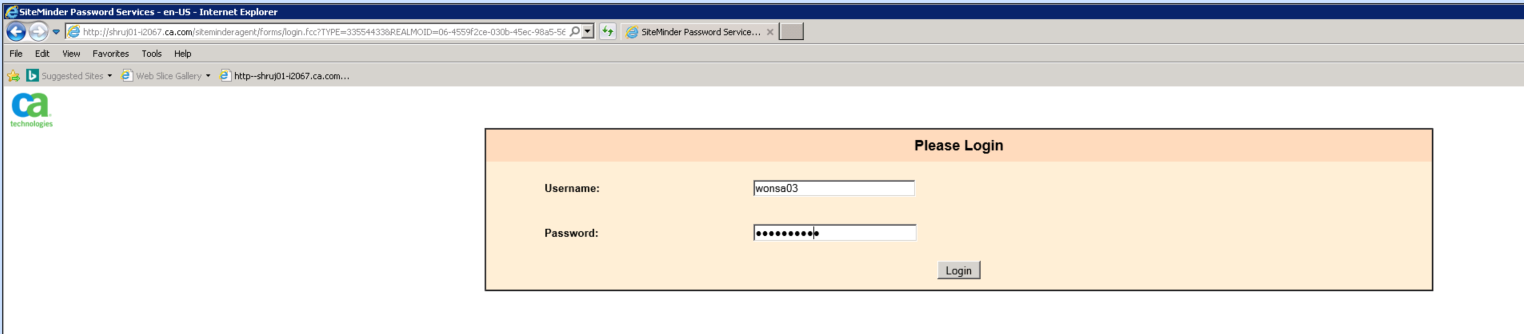
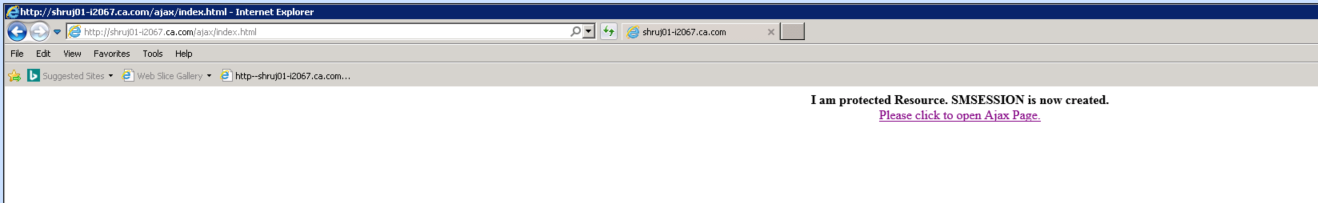
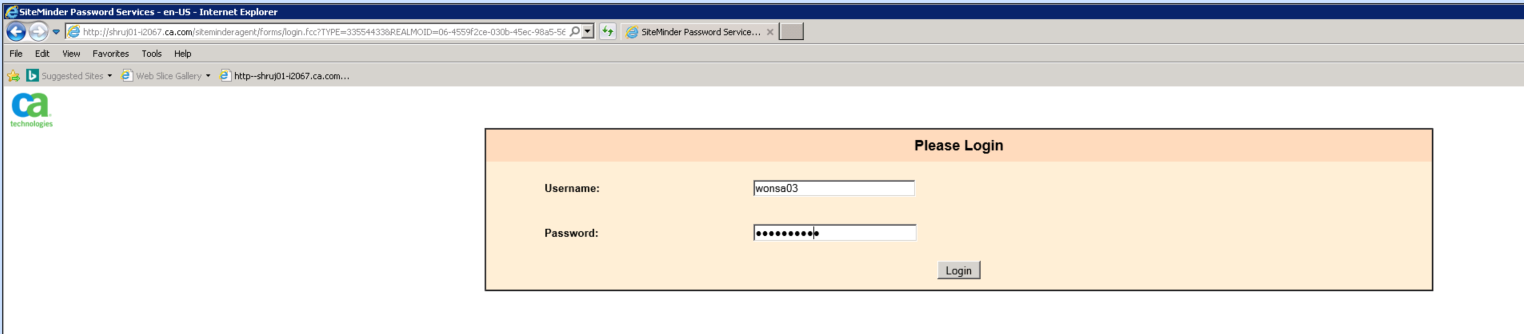
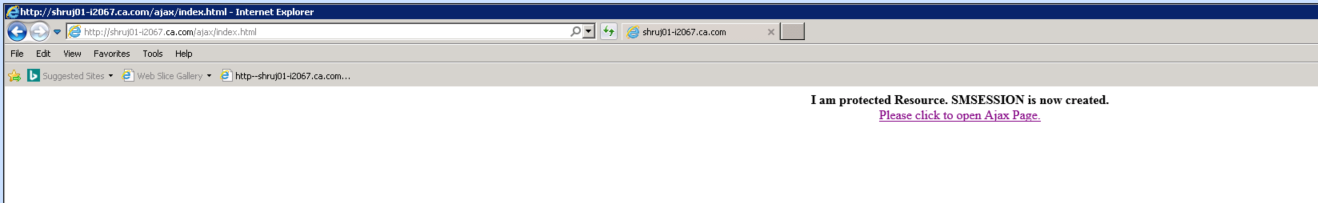
In this use case, we first login to the application by accessing protected resource.
Then, keep running the Ajax application until the idle time out (1 minute or as configured)
After the idle time out, CA SSO send the response as :
- Reason: IdleTimeout
- RedirectUrl : IdleTimeoutURL if configured otherwise blank
Ajax application then redirects as directed.

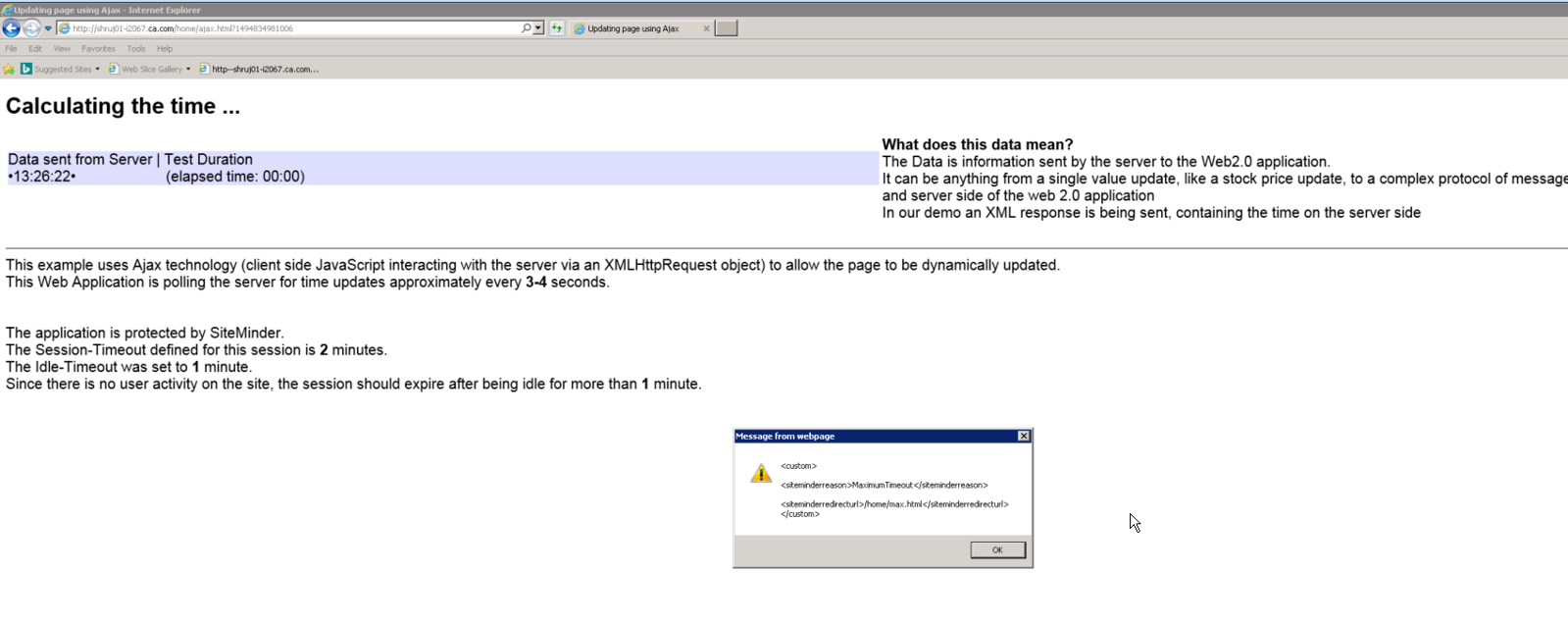
Use Case 3 : Maximum Timeout
In this use case, we first login to the application by accessing protected resource.
Then, pause the Ajax application (by not clicking OK on the popup window) , until the maximum time out is expired.
After the maximum time out, CA SSO send the response as :
- Reason: MaximumTimeout
- RedirectUrl : MaximumTimeOutURL if configured otherwise blank
Ajax application then redirects as directed.

Note :
It's very common for web server/browser to cache the html/ajax resources. Caching can lead to many unexpected results. So you will need ensure that the Ajax container page (ajax.html) and the ajax response itself are never cached.
In the sample application we have achieved this by appending the random query parameter based on the system time to the Ajax request (time.pl) as well as for the page containing the ajax script (ajax.html)
xmlhttp.open('GET', "/cgi-bin/time.pl?"+new Date().getTime(), false);
<BODY>
<center><B>I am protected Resource. SMSESSION is now created.</B></center>
<center><a href="/home/ajax.html" onClick="this.href=this.href.split('?')[0]+'?'+new Date().getTime()">Please click to open Ajax Page.</a></center>
</BODY>
</HTML>
Update 22/5/2017 : The XmlHttpRequest sample does work only in Internet Explorer. Firefox and Chrome browser doesn't seem to support it anymore. So, rewrote the Web 2.0 sample app using jQuery which has been verified to be working in IE/FF/Chrome. Depending on what browser you intend to test with, choose appropriate sample.