
Ransomware was a phenomenon that first emerged in Europe and then spread throughout the world. Primarily, the focus had been on affluent and English-speaking regions of the world. But increasingly we have seen cybercriminals turn their attention to countries in the Far East.
Moving to target a Far Eastern market does present some problems. Many citizens of the Far East do not understand English and if presented with a ransom message in a foreign language, may not understand the ransom message. So recognizing that there is a huge potential in countries like Korea and Japan to extract ransom payments from, the cybercriminals have taken the step to localize their ransomware for Far Eastern languages from this region. For example, in December 2014 we saw the first confirmed ransomware designed specifically to target Japanese-speaking users—a variant of TorLocker detected by Symantec as Trojan.Cryptolocker.
Now as further sign of this shift in strategy, we have seen another new ransomware variant, calling itself Crypt0L0cker (detected as Trojan.Cryptolocker.F). This has been found to be customized for at least two East Asian countries. The infection method used is drive-by-download typically through the use of exploit kits.
Learning new languages
Once a computer is compromised, the ransomware displays a localized message, the language used is dependent on the location of the compromised computer’s IP address.
Localized ransomware messages in various languages in Europe are common, but this may be one of the first—along with the TorLocker variant mentioned previously—to be localized in languages of counties located in the Far East.
If the ransomware infects a computer in an unspecified country, it will typically display the message in English.

Figure 1. Ransom message shown on a compromised computer in Singapore
However, if the malware is executed on a computer located in Japan or Korea, the messages are displayed in Japanese or Hangul respectively.

Figure 2. Ransom message shown on a compromised computer in Japan
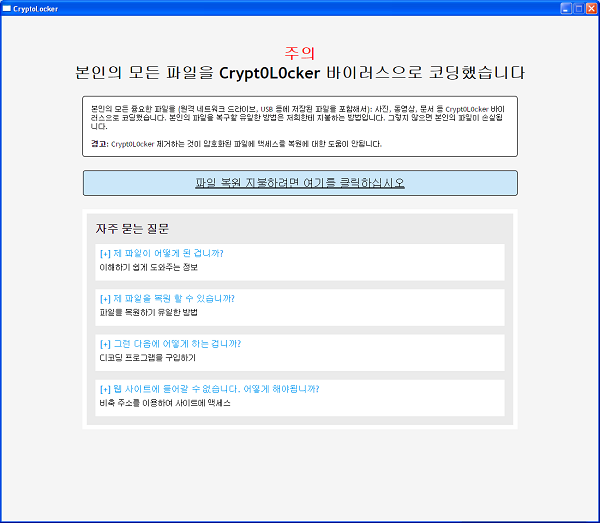
Figure 3. Ransom message shown on a compromised computer in Korea
The Japanese and Korean messages appear to have been written, potentially, by a non-native speaker or by using automated online translation services, this suggests that the attacker is not native or located outside of these countries.
Once the link to pay for the file recovery is clicked, the user is taken to a payment site where they are asked to pay 1.8 bitcoins (approximately US$400 at current exchange rates).

Figure 4. Payment page demanding 1.8 bitcoins
Countries targeted
A breakdown of the countries being targeted by this variant shows Korea with the majority of the attacks, with Japan and Malaysia sharing the remainder.

Figure 5. Countries being targeted by Trojan.Cryptolocker.F
The emergence of ransomware attacks specifically targeting Far Eastern countries is significant as it shows that attackers are waking up to the vast potential of these markets and the increasing wealth of this region. Language may have been a barrier to entry in the past but this is no longer the case.
Although this attack campaign is limited in scope compared to typical ransomware attacks observed worldwide, it is early days for this variant and there is every chance it could one day rival other ransomware attacks. Based on what we have seen so far, expansion to support other major Far Eastern languages and markets is almost inevitable.
Protection
Symantec has the following recommendations to help avoid or mitigate ransomware infections:
- Update the software, operating system, and browser plugins on your computer to prevent attackers from exploiting known vulnerabilities.
- Use comprehensive security software, such as Norton Security, to protect yourself from cybercriminals.
- Regularly back up any files stored on your computer. If your computer has been compromised with ransomware, then these files can be restored once the malware is removed from the computer.
- Never pay the ransom. There’s no guarantee that the attacker will decrypt the files as promised once they receive payment.
Symantec and Norton products detect all of the ransomware variants discussed in this blog as Trojan.Cryptolocker.F.