
The exposure of sensitive or compliance related documents in the cloud has become one of the primary data security threats that organizations face today. Leakage of these documents, intentional or otherwise, can be potentially disastrous for an organization and result in compliance fines, mitigation costs, and loss of customer trust. The problem is not specific to a single cloud app provider but can occur when using any file sharing app. Whether an exposure happens to just a handful of documents or millions, the damage can be severe. For instance, the loss of a single document containing a confidential business strategy can provide a significant edge to the competition, resulting in lost business opportunities and potential revenue.
Recently, the Symantec Cloud Threat Labs team discovered a number of invoice documents that were exposed via AWS S3 buckets. Due to responsible disclosure and ethical guidelines, we are not divulging the names of the involved businesses. These documents were publicly available and could be easily accessed and downloaded using a web browser. In an earlier blog, we discussed how globally accessible AWS buckets could lead to data exposure involving sensitive documents if not audited completely.
This incident highlights the importance of securing data in AWS buckets by restricting privileges. Considering the competitive nature of service providers, disclosure of invoices could be very damaging to an organization if discovered by external parties. For example, one of the invoice documents reveals information about a firm’s consulting services, associated costs, and its Tax Identification Number (TIN) as shown below:
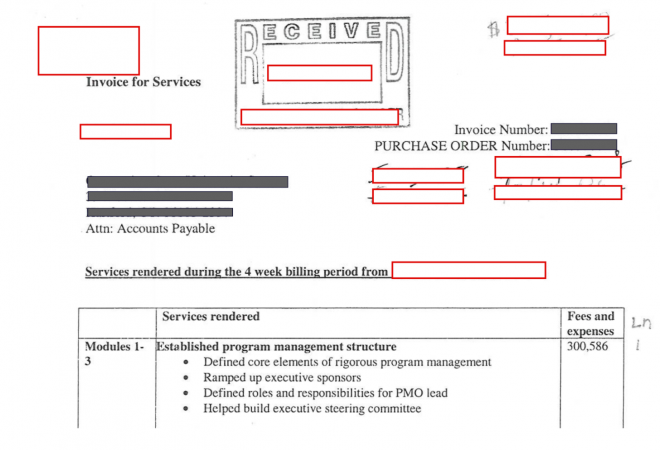 Figure 1: Invoice disclosing business consulting charges
Figure 1: Invoice disclosing business consulting charges
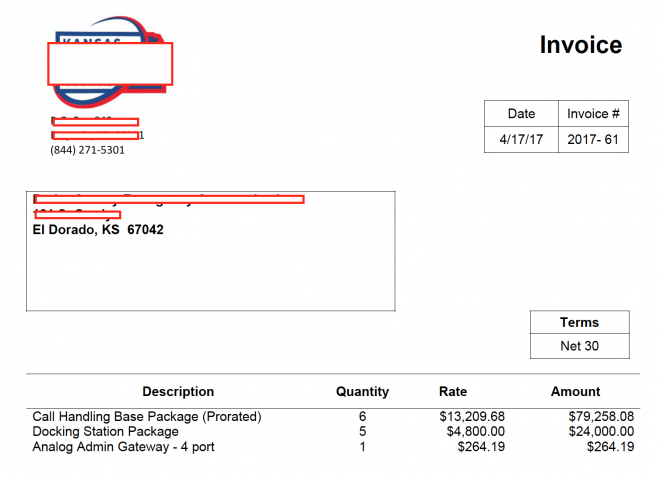 Figure 2: Invoice disclosing service and product costs
Figure 2: Invoice disclosing service and product costs
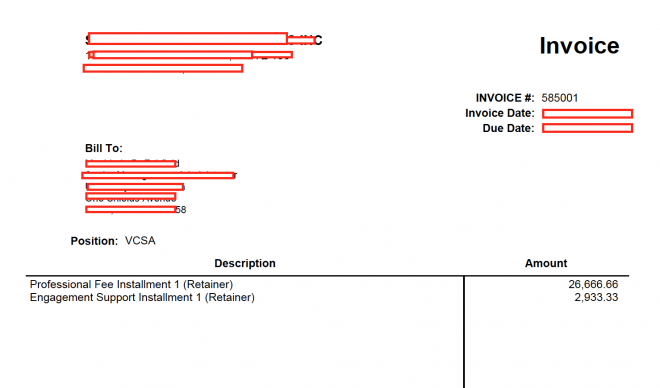 Figure 3: Invoice disclosing professional fees charged for a specific engagement
Figure 3: Invoice disclosing professional fees charged for a specific engagement
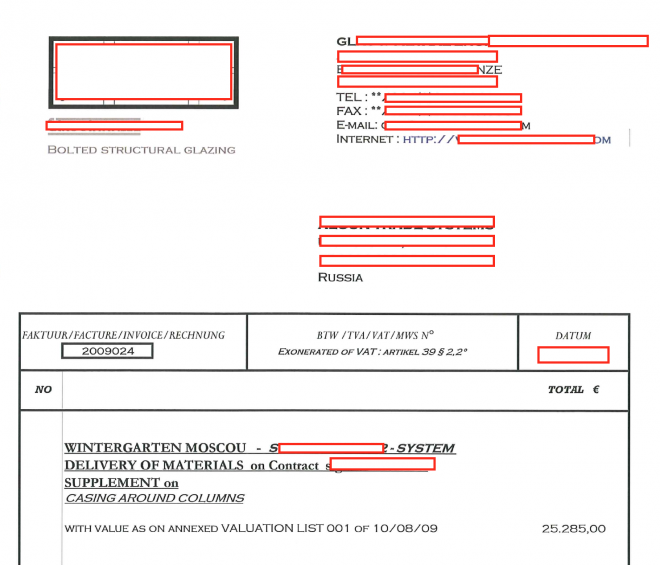 Figure 4: Invoice disclosing supply chain and delivery costs
Figure 4: Invoice disclosing supply chain and delivery costs
If documents like the ones above were exposed, the results could be devastating from a business perspective. The potential repercussions of this exposure are clear, and below we list only a few that can damage the business and benefit the competition (or attackers):
-
Glean more information about the different types of services being offered.
-
Understand the different types of fees being charged by the company for specific services.
-
Collect sensitive information such as Tax Identification Number (TIN).
-
Understand the revenue generation model being followed by the company.
-
Underbid the company on RFPs to win projects.
Considering the above case studies, there are several points to ponder:
-
Are the documents being exposed by the business firms’ clients by mistake?
-
Are the documents being exposed by a malicious insider who wants to make the sensitive information public?
-
What would be the impact on the business if the documents were exposed and accessed by competitors?
-
Do the involved parties have a Cloud Access Security Broker (CASB) solution to monitor the activities in the cloud, analyze exposed content, and alert or remediate a business-sensitive exposure?
As discussed earlier, exposure of sensitive documents in the cloud can have a substantial impact on the businesses irrespective of the sources and causes of the exposure. Considering the case discussed here, it shows how crucial it has become for an organizations to deploy to uncover and classify sensitive corporate data and then enable the organization to set policies around its use and sharing.