Introduction:
Enterprises today are faced with a dilemma. How do they enable access to their users from anywhere on any device thereby enhancing user convenience while lowering security risk and keeping costs in check?
CA Advanced Authentication offers a flexible and scalable solution that incorporates behavior and credential based authentication methods that allows enterprises to meet regulatory requirements in authenticating employees, partners and consumers while providing a simple user experience, higher security and lower total cost of ownership (TCO). The solution covers both conventional use cases like web portals, VPN and the rapidly expanding user cases of Mobile and IoT.
Summary of Findings:
The test client simulates the work load from the customer’s web infrastructure by making calls to the APIs from a test driver that invokes the following APIs of the Risk and Strong Auth Servers in order to
perform the authentication requests. These are the APIs called in a typical deployment of the product when using risk-based assessment and the 2-factor CA Auth ID™ credential.
- EvaluateRisk (Sent to the CA Risk Authentication Server, which then evaluates the risk using both the behavior model and rules, calculates a risk score, and recommends action)
- GetChallenge (Sent to retrieve the challenge from the CA Strong Authentication Server)
- SignChallenge (This happens on the client and hence is not counted in the measurement)
- VerifySignChallenge (Sent to verify the signed challenge returned by the client)
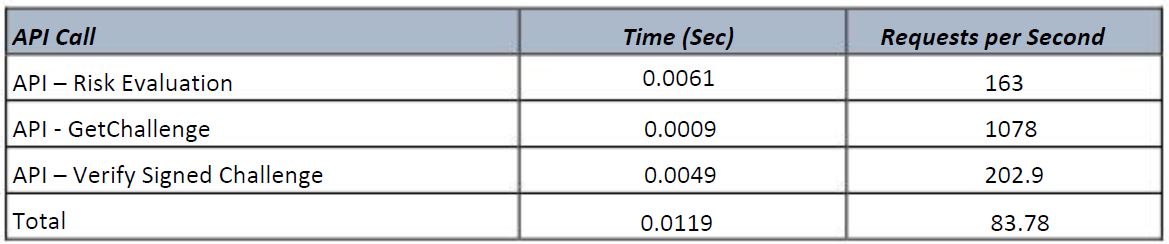
These APIs are called in sequence to complete a single authentication. Discarding any network latency and delays in client side processing, CA Advanced Authentication Servers delivers a throughput of 84
Requests per second. The response time for these requests ranges from 0.9 to 6.1 milliseconds when measured on the server. The figure below highlights that these response times are done at less than
20% CPU utilization.

Conclusion:
CA Advanced Authentication Server is able to deliver excellent results in an environment demanding high performance while providing the robust security of two-factor authentication.
Please find the attached performance measurement report.