Hi
Running individual operation against the provisioning server like explore & correlate seems like a impossible task on large environment with large numbers of users. usually, if you want to test a change from an endpoint, you will need to full E&C the endpoint. well, the following article will expalin how, by using simple LDAP calls with the DXSEARCH command, you will be able to do just that.
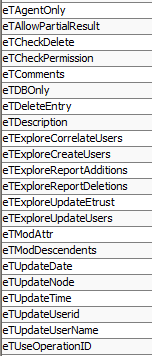
You can invoke multiple operation on the provisioning server using the dxsearch command. By using customize LDAP search commands and using some operational attributes (see below) as the return attributes.
In order to use this “trick” you should connect to the Router DSAs (port 20389/20390) .
The following are examples of the most common usage for these commands
Explore operation:
dxsearch -D "eTGlobalUserName=imadmin,eTGlobalUserContainerName=Global Users,eTNameSpaceName=CommonObjects,dc=im,dc=eta" -w xxxxx -x -h xxxxx -p 20389 -s sub -b "eTDYNAccountName=*,eTDYNContainerName=FD-USA,eTDYNDirectoryName=RSA-PROD,eTNameSpaceName=RSA SecurID 7,dc=im,dc=eta" eTExploreUpdateEtrust
Explanation:
- This is a simple dxsearch command but the parameters determine what the provisioning actually do. In this case, the usage of the eTExploreUpdateEtrust attribute will cause it to run an explore operation
- The base DN (-b operator) need to point to the account DN in the provisioning directory. In the above example will perform full Explore operation on a RSA endpoint on all accounts under the DS-USA container.
- In order to perform individual explore operation on one account, just change the –b parameter to point to the account. You will need to know the account DN of course but you can also use search critiria in order to perform the explore operation on multiple account, for example, if you put the value of -b "eTDYNAccountName=*itamar*,eTDYNContainerName=FD-USA,eTDYNDirectoryName=RSA-PROD,eTNameSpaceName=RSA SecurID 7,dc=im,dc=eta", the explore operation will work on all accounts where their account IDs have itamar in their name.
- Notice that I used the eTDYNAccountName attribute for this query, but you can use any attribute from the connector schema like first/last name etc.
Explore and Correlate operation:
dxsearch -D "eTGlobalUserName=imadmin,eTGlobalUserContainerName=Global Users,eTNameSpaceName=CommonObjects,dc=im,dc=eta" -w xxxxx -x -h xxxx -p 20389 -s sub -b "eTDYNContainerName=FD-USA,eTDYNDirectoryName=RSA-PROD,eTNameSpaceName=RSA SecurID 7,dc=im,dc=eta" (eTDYNAccountName=*) eTExploreCorrelateUsers
- The main differences between this command and the pervious one are:
o The –b should always point to the OU where you want to perform the operation. In this example, the E&C operation will run on the FD-USA container. In order to perform a full E&C, just use the endpoint DN from the provisioning directory (always connect to the router DSA)
o The (eTDYNAccountName=*) value will determine which accounts you will E&C, in this command all accounts, as before, you can manipulate the search parameter to individually E&C accounts.
o The eTExploreCorrelateUsers return attribute is the operational attribute that will trigger E&C operation
Other operation:
You can find other operations under the eTSystemSettingsContainerName=System Settings,eTNamespaceName=CommonObjects,dc=eta OU. I didn’t used the others but feel free to test them
I hope this helps
Itamar