I am configuring CA SSO OpenID Connect Provider with Apache open ID client using doc - CA SSO OpenID Connect Provider - with Apache OpenID Client
below are details of my infrastructure -
RHEL 7.4
Policy Server R12.7
Access Gateway R12.7
Installed Apache 2.4
Installed mod_auth_openidc
OpenIDC Client : http://*********.xxxx.******/example/redirect
OpenIDC Connect Provider : http://******.xxxx.xxxx/affwebservices/secure/secureredirect
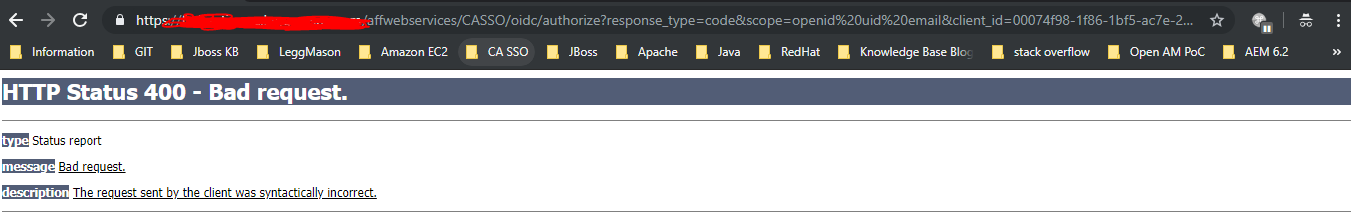
when I access URL openIDC client side http://*********.xxxx.******/example/index.html page I get error 400 bad request
below are the logs I get in spstrace and policy server trace logs
Policy server trace logs
[11/22/2018][06:48:07.257][IsProtected.cpp:98][CSm_Az_Message::IsProtected][13286][140130924869376][][][][fed_qa_dmz][][][][][][][][][GET][/affwebservices/CASSO/oidc/authorize?response_type=code&scope=openid%20uid%20email&client_id=00074f98-1f86-1bf5-ac7e-2de60a690000&state=EIZTCaUhTrzUjaHlRl7Q7RAulmM&redirect_uri=http%3A%2F%2Fabc.pqr.com%3A8001%2Fexample%2Fredirect&nonce=DJa-j41HoGKzw7NKwP6b4QSKbyMbWYw7A0W75uTxIOM][][][][][Starting IsProtected processing.][][][][][]
[11/22/2018][06:48:07.257][SmAuthorization.cpp:642][CSmAz::IsProtected][13286][140130924869376][][][][][][][][][][][][][][/affwebservices/casso/oidc/authorize?response_type=code&scope=openid%20uid%20email&client_id=00074f98-1f86-1bf5-ac7e-2de60a690000&state=eiztcauhtrzujahlrl7q7raulmm&redirect_uri=http%3a%2f%2fabc.pqr.com%3a8001%2fexample%2fredirect&nonce=dja-j41hogkzw7nkwp6b4qskbymbwyw7a0w75utxiom][][][][][Not Protected: No matching rules found for resource.][][][][][]
SPS trace log
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][CSmSessionManager::EstablishSession][SM_WAF_HTTP_PLUGIN->EstablishSession returned SmNoAction.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][CSmSessionManager::EstablishSession][Calling SM_WAF_AG_PLUGIN->EstablishSession.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][CSmSessionManager::EstablishSession][SM_WAF_AG_PLUGIN->EstablishSession returned SmNoAction.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][IsResourceProtected][Resource is not protected from Policy Server.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][ProcessResponses][Calling SM_WAF_HTTP_PLUGIN->ProcessResponses.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][CSmHttpPlugin::ProcessResponses][Processing IsProtected responses.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][ProcessResponses][SM_WAF_HTTP_PLUGIN->ProcessResponses returned SmSuccess.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][ProcessResponses][Calling SM_WAF_AG_PLUGIN->ProcessResponses.]
[11/22/2018][06:48:07][16190][140013987833600][299477e5-df7513c7-c46d9a4c-8c475fe9-7534df75-a0][ProcessResponses][SM_WAF_AG_PLUGIN->ProcessResponses returned SmNoAction.]
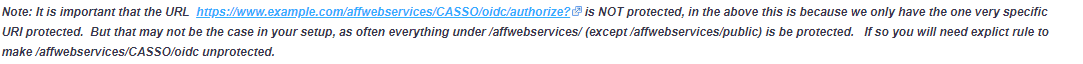
I noticed below point from doc so I unprotected /affwebservices/CASSO/oidc/ in realm but still instead of showing login pop-up it directly thows 400 bad request error
Below is my apache oidc module configuration -
OIDCSSLValidateServer Off
OIDCProviderIssuer https://xyz.abc.com
OIDCClientID ***************************
OIDCClientSecret xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
OIDCProviderAuthorizationEndpoint https://xyz.abc.com/affwebservices/CASSO/oidc/authorize
OIDCProviderTokenEndpoint https://xyz.abc.com/affwebservices/CASSO/oidc/token
OIDCRedirectURI http://abc.pqr.com:8001/example/redirect
OIDCCryptoPassphrase *********
OIDCProviderTokenEndpointAuth client_secret_post
OIDCProviderJwksUri https://xyz.abc.com/affwebservices/CASSO/oidc/jwks?AuthorizationProvider=ABCCorp
OIDCScope "openid uid email"
OIDCProviderUserInfoEndpoint https://xyz.abc.com/affwebservices/CASSO/oidc/userinfo
<Location /example/>
AuthType openid-connect
Require valid-user
</Location>
AddHandler cgi-script .bat
Options +Indexes +FollowSymLinks +ExecCGI
Can someone please help me where I am missing ?
Regards
Prashant