Luiz,
First, from the look of your watch, if using "ifAdminStatus.#" in your expression, I am assuming you are creating the watch on the device model, correct? If so, you have to be very careful with SpectroWatches as they are very expensive in terms of memory and CPU required to process them. The more watches on more models the more of a performance hit on the SpectroSERVER.
Using "ifAdminStatus.#" in your expression will cause the watch to check ALL instances of ifAdminStatus in the interfaces mib. If the device has a lot of interfaces configured, this could also cause a significant performance hit on the device. If this watch is active on many models, you could cause a serious performance issue with the SpectroSERVER.
We need to find some way to limit either the number of devices you create the watch on or the number of interfaces you want to check the status of ifAdminStatus on so you do not run into any of these possible performance issues with the SpectroSERVER or the device.
This can be done by using Global Collections and the Policy Manager.
If the watch has to be on the device model, create a Global Collection populated with only those device model where the watch needs to be created. Create the watch but Inactive by default. Then create a Policy which will activate the watch on only those models contained within the Global Collection. This is documented in detail in the Policy Manager section of the documentation.
If you can create a Global Collection that contains only the interface models you want to check for the status of ifAdminStatus, you can create the watch on the interface model Inactive by default and then create a Policy which will activate the watch on only those models contained within the Global Collection.
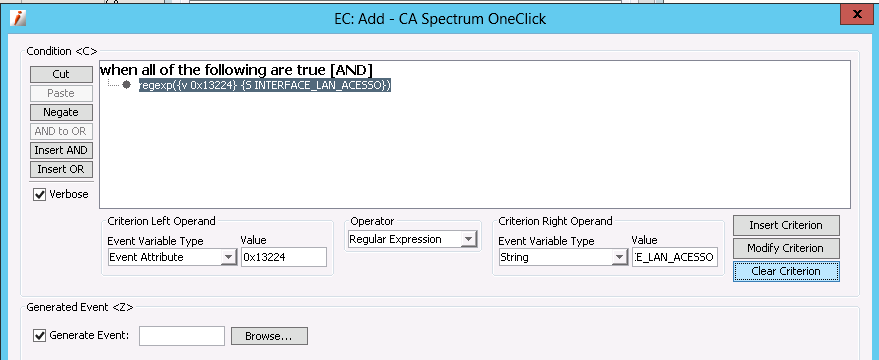
As for checking the value of ifAlias, if creating the watch on interface models contained within a Global Collection, you may be able to use the Search Criteria for the Global Collection to not include those models. If not, you will need to create an Event Condition rule to check the value of X_ifAlias attribute id 0x13224. The reason I recommend using X_ifAlias is because it is an internal database attribute where ifAlias is an external attribute where Spectrum will have to do an snmpget to get the value. The Condition Rule would looks something like the following:
If you have to use the device, then getting the value of ifAlias for the interface is going to be more difficult. You would have to use ifAlias you could not use X_ifAlias. In addition, you would have to have a way to get the value if ifAlias for the same instance in the interfaces table as ifAdminStatus. For that you would need to attach an Event Procedure to event generated from the watch. This again, adding to the resources requirements in order to get the results you are looking for.
Joe