Issue/Problem/Symptoms:
This document will provide step by step guide to configure Enhanced Session Assurance with DeviceDNA™ functionality.
Environment:
- CA Access Gateway (formerly CA Secure Proxy Server ) : R12.52SP1 and above
- Policy Server : R12.52SP1 and above
Pre-requisites:
Policy Server
- Ensure "CA RiskMinder" ( Advanced Authentication ) service is up and running on the Policy Server.
Tip:
Check Service Console.
Check <PolicyServer_Install_Directory>\CA\aas\logs\cariskminderstartup.log
The log should say:
"CA RiskMinder Service READY"
- Ensure that you have installed and configured Session Store.
CA Access Gateway Server (formerly CA Secure Proxy Server)
- Ensure that you have configured CA Access Gateway server to use SSL (Only front end Apache is sufficient)
- Ensure that you can telnet from CA Access Gateway server to Policy server on port 7680
- Ensure that JCE ( Java Cryptography Extension (JCE) Unlimited Strength Jurisdiction Policy Files ) patch is applied on the JRE used by CA Access Gateway server.
- Ensure "CA Advanced Authentication Flow Application" ( Advanced Authentication ) service is up and running on the CA Single Sign-On CA Access Gateway Server.
This could be verified by accessing following URL :
https://<CA_Access_Gateway_Server_FQDN>:<SSL_PORT>/uiapp/
You should get a page similar to below. (Ignore the error, as it is just indicating that the required parameter is not being passed)
Instructions:
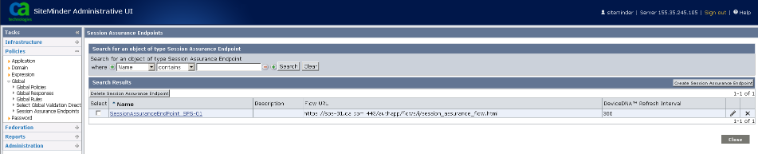
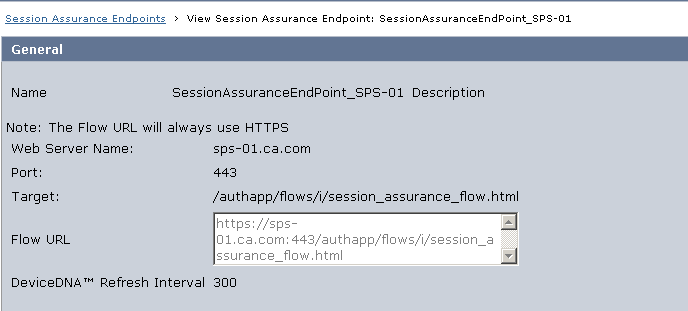
- Create Enhanced Session Assurance end points
From Administrative UI, click Policies-->Global-->Session Assurance Endpoints.
- Add Session Assurance End Point to your realm
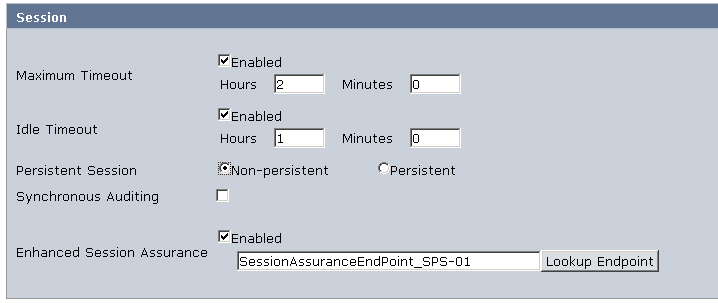
Note : For Session Assurance to work it is NOT necessary to enable Persistent Session on the realm.
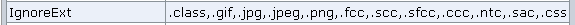
- Ensure that the ACO used by your CA Access Gateway server has ".sac" extension included in the IgnoreExt ACO parameter
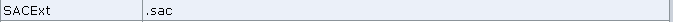
- Ensure that ACO used by your CA Access Gateway has the SACExt parameter set to ".sac" as below :
Testing:
Sample working fiddler trace is attached - SessionAssurance_Working.saz
Additional Information:
- As the FLOW App on the CA Access Gateway is a local app deployed as web app on the Tomcat server, you do not need to configure any proxy rules in the Proxyrules.xml pertaining to the session assurance.
- How to configure SSL on CA Access Gateway
Configuring SSL for CA SiteMinder® SPS
- CA Single Sign-On Bookshelf intro on Session Assurance Configuration
https://docops.ca.com/ca-single-sign-on-12-52-sp1/en/configuring/policy-server-configuration/enhanced-session-assurance-…