Hi Im trying to federate Shibbolet SP with CA SSO as IDP.
I generated the identity in CA SSO

I configured shibbolet
<SPConfig xmlns="urn:mace:shibboleth:2.0:native:sp:config"
xmlns:conf="urn:mace:shibboleth:2.0:native:sp:config"
xmlns:saml="urn:oasis:names:tc:SAML:2.0:assertion"
xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"
xmlns:md="urn:oasis:names:tc:SAML:2.0:metadata"
clockSkew="180">
<InProcess logger="native.logger">
<ISAPI normalizeRequest="true" safeHeaderNames="true">
<!--
Maps IIS Instance ID values to the host scheme/name/port. The name is
required so that the proper <Host> in the request map above is found without
having to cover every possible DNS/IP combination the user might enter.
-->
<Site id="1" name="sm.lab.com"/>
<!--
When the port and scheme are omitted, the HTTP request's port and scheme are used.
If these are wrong because of virtualization, they can be explicitly set here to
ensure proper redirect generation.
-->
<!--
<Site id="42" name="virtual.example.org" scheme="https" port="443"/>
-->
</ISAPI>
</InProcess>
<RequestMapper type="Native">
<RequestMap>
<!--
The example requires a session for documents in /secure on the containing host with http and
https on the default ports. Note that the name and port in the <Host> elements MUST match
Apache's ServerName and Port directives or the IIS Site name in the <ISAPI> element above.
-->
<Host name="sm.lab.com">
<Path name="secure" authType="shibboleth" requireSession="true"/>
</Host>
<!-- Example of a second vhost mapped to a different applicationId. -->
<!--
<Host name="admin.example.org" applicationId="admin" authType="shibboleth" requireSession="true"/>
-->
</RequestMap>
</RequestMapper>
<!--
U-M shibboleth documentation can be found at
http://documentation.its.umich.edu/shibboleth
-->
<!--
By default, in-memory StorageService, ReplayCache, ArtifactMap, and SessionCache
are used. See example-shibboleth2.xml for samples of explicitly configuring them.
-->
<!--
To customize behavior for specific resources on Apache, and to link vhosts or
resources to ApplicationOverride settings below, use web server options/commands.
See https://wiki.shibboleth.net/confluence/display/SHIB2/NativeSPConfigurationElements for help.
For examples with the RequestMap XML syntax instead, see the example-shibboleth2.xml
file, and the https://wiki.shibboleth.net/confluence/display/SHIB2/NativeSPRequestMapHowTo topic.
-->
<!-- The ApplicationDefaults element is where most of Shibboleth's SAML bits are defined. -->
<ApplicationDefaults entityID="smidp"
REMOTE_USER="eppn persistent-id targeted-id">
<!--
Controls session lifetimes, address checks, cookie handling, and the protocol handlers.
You MUST supply an effectively unique handlerURL value for each of your applications.
The value defaults to /Shibboleth.sso, and should be a relative path, with the SP computing
a relative value based on the virtual host. Using handlerSSL="true", the default, will force
the protocol to be https. You should also set cookieProps to "https" for SSL-only sites.
Note that while we default checkAddress to "false", this has a negative impact on the
security of your site. Stealing sessions via cookie theft is much easier with this disabled.
-->
<Sessions lifetime="28800" timeout="3600" relayState="ss:mem"
checkAddress="false" handlerSSL="false" cookieProps="https">
<!--
Configures SSO for a default IdP. To allow for >1 IdP, remove
entityID property and adjust discoveryURL to point to discovery service.
(Set discoveryProtocol to "WAYF" for legacy Shibboleth WAYF support.)
You can also override entityID on /Login query string, or in RequestMap/htaccess.
-->
<SSO entityID="smidp"
discoveryProtocol="SAMLDS" discoveryURL="https://ds.example.org/DS/WAYF">
SAML2 SAML1
</SSO>
<!-- SAML and local-only logout. -->
<Logout>SAML2 Local</Logout>
<!-- Extension service that generates "approximate" metadata based on SP configuration. -->
<Handler type="MetadataGenerator" Location="/Metadata" signing="false"/>
<!-- Status reporting service. -->
<Handler type="Status" Location="/Status" acl="127.0.0.1 ::1"/>
<!-- Session diagnostic service. -->
<Handler type="Session" Location="/Session" showAttributeValues="false"/>
<!-- JSON feed of discovery information. -->
<Handler type="DiscoveryFeed" Location="/DiscoFeed"/>
</Sessions>
<!--
Allows overriding of error template information/filenames. You can
also add attributes with values that can be plugged into the templates.
-->
<Errors supportContact="root@localhost"
helpLocation="/about.html"
styleSheet="/shibboleth-sp/main.css"/>
<!-- Example of remotely supplied batch of signed metadata. -->
<!--
<MetadataProvider type="XML" uri="http://federation.org/federation-metadata.xml"
backingFilePath="federation-metadata.xml" reloadInterval="7200">
<MetadataFilter type="RequireValidUntil" maxValidityInterval="2419200"/>
<MetadataFilter type="Signature" certificate="fedsigner.pem"/>
</MetadataProvider>
-->
<!-- UMich Production metadata -->
<!-- Obtain the U-M metadata signing certificate from https://shibboleth.umich.edu/md/umich-md-sign.pem -->
<!--
<MetadataProvider type="XML" uri="https://shibboleth.umich.edu/md/umich-prod-idps.xml"
backingFilePath="umich-prod-idps.xml" reloadInterval="7200">
<MetadataFilter type="Signature" certificate="umich-md-sign.pem"/>
<MetadataFilter type="Whitelist">
<Include>https://shibboleth.umich.edu/idp/shibboleth</Include>
</MetadataFilter>
</MetadataProvider>
-->
<!-- UMich Non-production metadata -->
<!-- Obtain the U-M metadata signing certificate from https://shibboleth.umich.edu/md/umich-md-sign.pem -->
<!--
<MetadataProvider type="XML" uri="https://shibboleth.umich.edu/md/umich-nonprod-idps.xml"
backingFilePath="e:/umich-nonprod-idps.xml" reloadInterval="7200">
<MetadataFilter type="Signature" certificate="umich-md-sign.pem"/>
</MetadataProvider>
-->
<!--
<MetadataProvider type="XML"
uri="https://shibboleth.umich.edu/md/umich-nonprod-idps.xm"
backingFilePath="e:\\umich-nonprod-idps.xml" reloadInterval="7200">
<MetadataFilter type="Signature" certificate="umich-md-sign.pem"/>
<MetadataFilter type="Whitelist">
<Include>https://shibboleth.umich.edu/idp/shibboleth</Include>
</MetadataFilter>
</MetadataProvider>
-->
<!--
<MetadataProvider type="XML"
uri="https://shibboleth.umich.edu/md/umich-nonprod-idps.xml"
file="e:\\umich-nonprod-idps.xml" >
</MetadataProvider>
-->
<MetadataProvider type="XML" file="e:\\smidpMetadata.xml" >
</MetadataProvider>
<!-- InCommon metadata -->
<!-- obtain the InCommon cert from https://spaces.internet2.edu/display/InCFederation/Metadata+Signing+Certificate -->
<!--
<MetadataProvider type="XML" uri="http://md.incommon.org/InCommon/InCommon-metadata.xml"
backingFilePath="InCommon-metadata.xml" reloadInterval="7200">
<MetadataFilter type="Signature" certificate="inc-md-cert.pem"/>
</MetadataProvider>
-->
<!-- Example of locally maintained metadata. -->
<!--
<MetadataProvider type="XML" file="partner-metadata.xml"/>
-->
<!-- Map to extract attributes from SAML assertions. -->
<AttributeExtractor type="XML" validate="true" reloadChanges="false" path="attribute-map.xml"/>
<!-- Use a SAML query if no attributes are supplied during SSO. -->
<AttributeResolver type="Query" subjectMatch="true"/>
<!-- Default filtering policy for recognized attributes, lets other data pass. -->
<AttributeFilter type="XML" validate="true" path="attribute-policy.xml"/>
<!-- Simple file-based resolver for using a single keypair. -->
<CredentialResolver type="File" key="sp-key.pem" certificate="sp-cert.pem"/>
<!--
The default settings can be overridden by creating ApplicationOverride elements (see
the https://wiki.shibboleth.net/confluence/display/SHIB2/NativeSPApplicationOverride topic).
Resource requests are mapped by web server commands, or the RequestMapper, to an
applicationId setting.
Example of a second application (for a second vhost) that has a different entityID.
Resources on the vhost would map to an applicationId of "admin":
-->
<!--
<ApplicationOverride id="admin" entityID="https://admin.example.org/shibboleth"/>
-->
<!--
For more information on configuring 2FA at U-M, please refer to the following documents:
Configuring Your Service Provider for Two-Factor Authentication
http://documentation.its.umich.edu/node/345
Configuring Your Service Provider for Step-Up Two-Factor Authentication
http://documentation.its.umich.edu/node/344
-->
<!-- Step-up 2-factor at U-M -->
<!--
<ApplicationOverride id="stepup2f">
<Sessions lifetime="28800" timeout="3600" checkAddress="false" handlerURL="/stepup/Shibboleth.sso" handlerSSL="false">
<SessionInitiator type="Chaining" Location="/SecureLogin" isDefault="false" id="mtoken" relayState="cookie" entityID="https://shibboleth.umich.edu/idp/shibboleth" authnContextClassRef="urn:oasis:names:tc:SAML:2.0:ac:classes:TimeSyncToken">
<SessionInitiator type="SAML2" template="bindingTemplate.html"/>
</SessionInitiator>
</Sessions>
</ApplicationOverride>
-->
</ApplicationDefaults>
<!-- Policies that determine how to process and authenticate runtime messages. -->
<SecurityPolicyProvider type="XML" validate="true" path="security-policy.xml"/>
<!-- Low-level configuration about protocols and bindings available for use. -->
<ProtocolProvider type="XML" validate="true" reloadChanges="false" path="protocols.xml"/>
</SPConfig>
I created the remote sp also in CA SSO

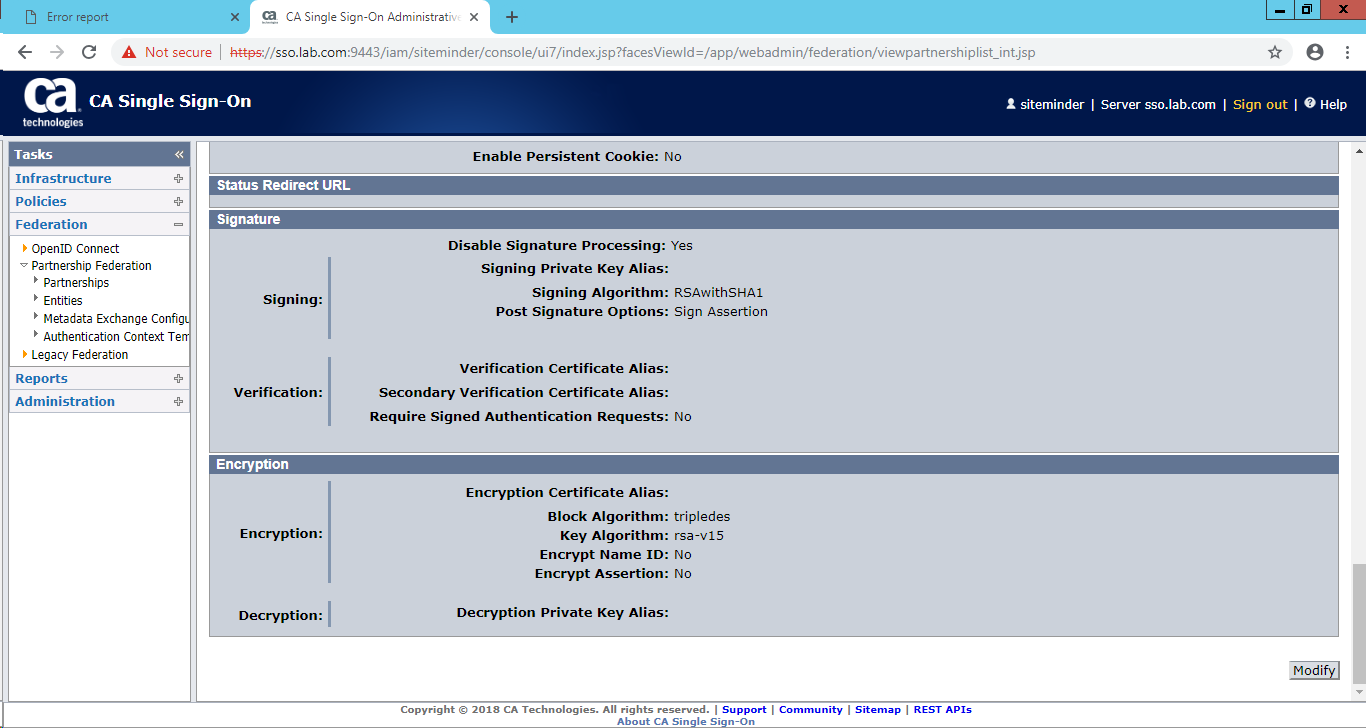
Created the federation partnership




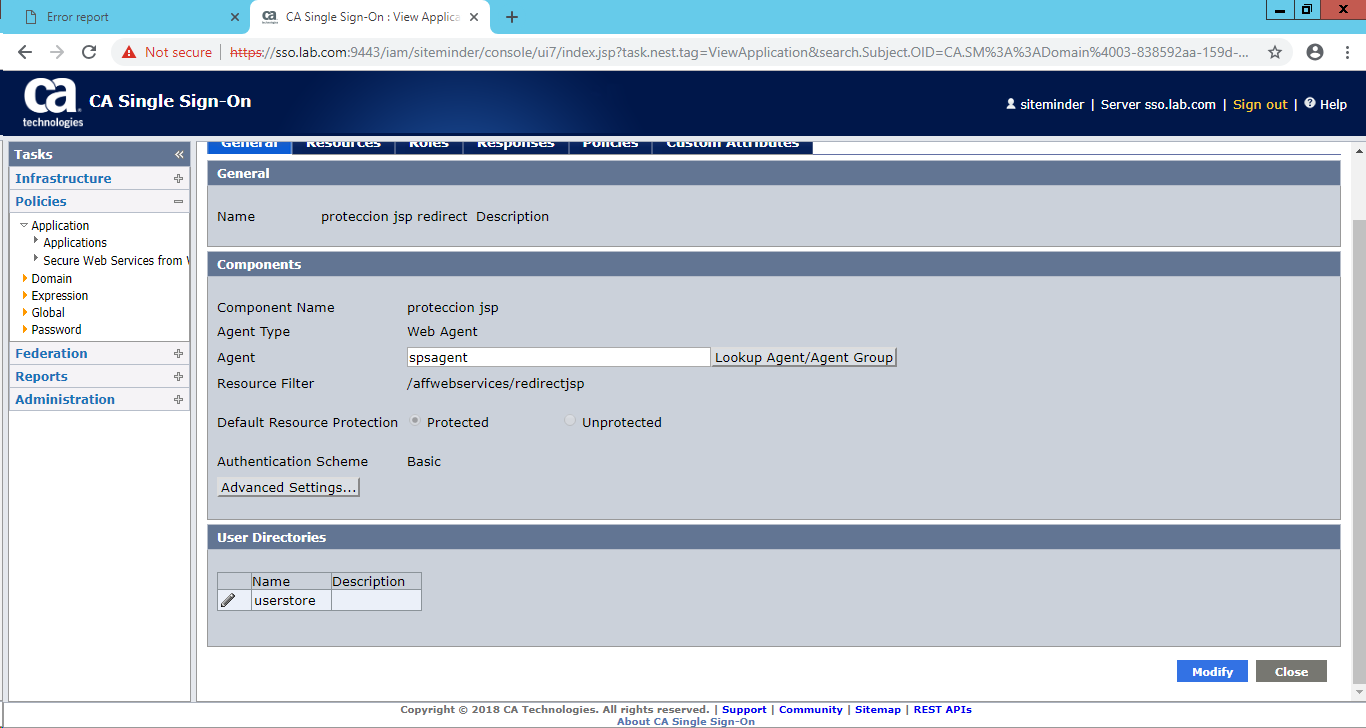
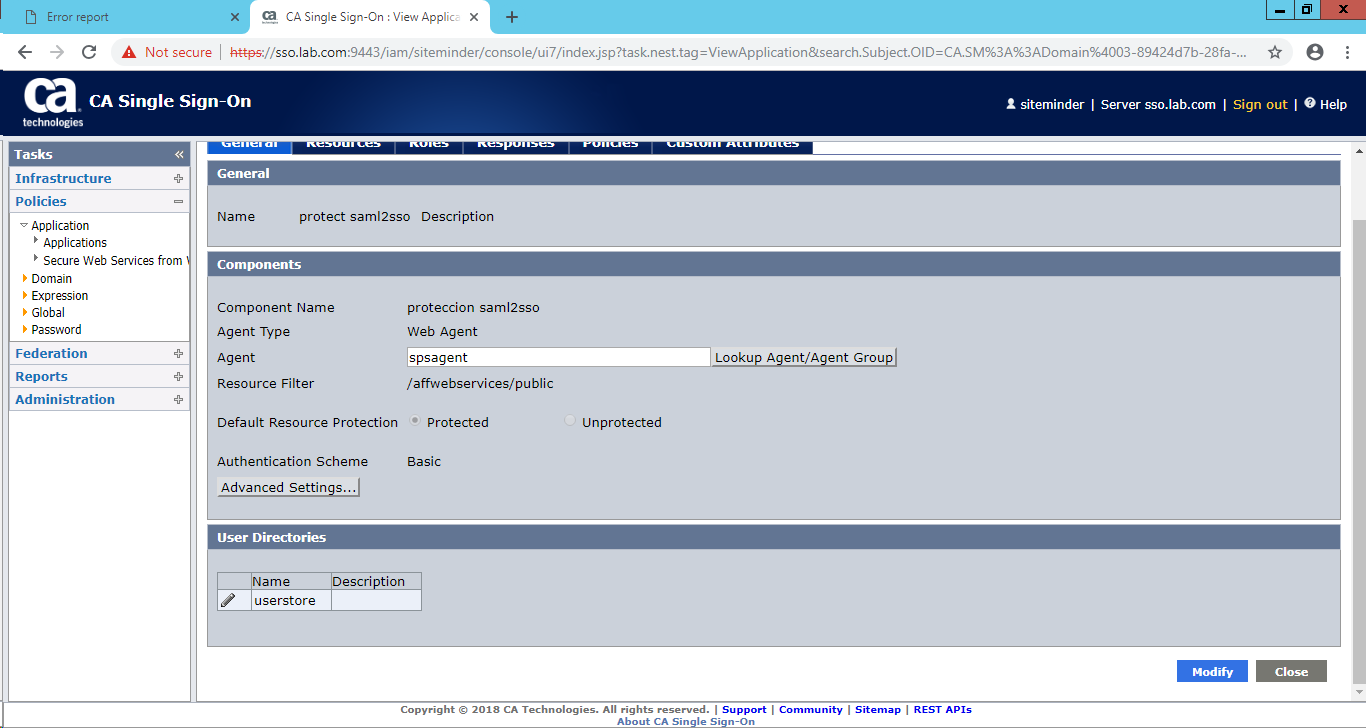
Im also protected the urls
http://accessg.lab.com:180/affwebservices/redirectjsp/redirect.jsp
and
http://accessg.lab.com:180/affwebservices/public/saml2sso
in the FWStrace.log
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SAMLTunnelClient.java][getServiceProviderInfoByID][Tunnel result code: 1.]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SAMLTunnelClient.java][getServiceProviderInfoByID][SAMLTunnelStatus: 5, Failed to obtain Service Provider data by provider ID. Provider ID: smidp]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SAML2Base.java][getServiceProviderInfo][SAML2.0 SP Configuration is not in cache. Requesting to get from policy server [CHECKPOINT = SSOSAML2_SPCONFFROMPS_REQ]]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SAML2Base.java][getServiceProviderInfo][Could not find service provider information for sp: smidp Message: Failed to obtain Service Provider data by provider ID. Provider ID: smidp.]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SAML2Base.java][getServiceProviderInfo][Could not find service provider information for idp: smidp.]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SSO.java][processRequest][Transaction with ID: 209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486 failed. Reason: NO_PROVIDER_INFO_FOUND]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SSO.java][processRequest][No SAML2 provider information found for SP smidp.]
[05/04/2019][01:31:52][1728][5848][209d04e6-1e273fcd-a98afb0e-09bc6f53-e0d06bbd-486][SSO.java][processRequest][Ending SAML2 Single Sign-On Service request processing with HTTP error 400]
I get this error
When I run
Shibbolet goes to the CA SSO IDP and request authentication
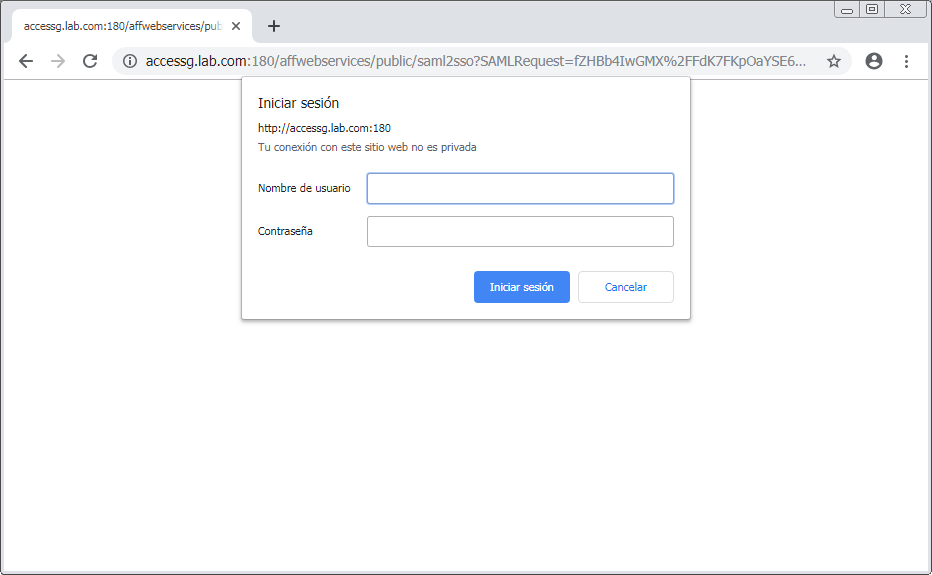
and after that
