Issue
On UNIX or Linux a privileged account can change the password of any other account by running a "sudo passwd <user>" command, assuming the privileged account is allowed to run "sudo passwd" per configuration in the /etc/sudoers file. The default Update Credentials Script for a target applications of type UNIX is written with that use case in mind.
The root account can run the passwd command without using sudo. However, the default script unconditionally uses the sudo command, or in general the Privilege Elevation Command configured in the target application, when the password change process for a target account is configured with the "Use the following account to change the password" flag. If the root account is configured in PAM as the account to update the password and there is no entry for the root user in the /etc/sudoers file to allow it to run a "sudo passwd" command, the password update attempt will fail. The tomcat log, which can be accessed from the Config > Diagnostics page, will show an exception similar to the following:
com.cloakware.cspm.server.plugin.ClientChannelTimeoutException: Failed to find regular expression pattern(s) while reading from the communications channel: [(?si)(.*?password(\sfor|:).*?)]"
Workaround/Solution
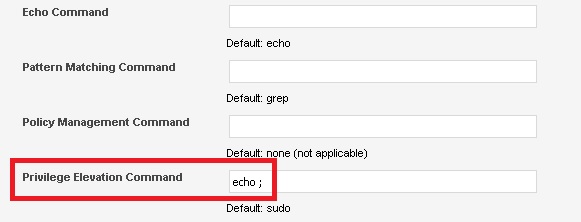
There are several ways to avoid this problem. The most obvious one is to allow root to run a "sudo passwd" command. An alternative is to configure a privileged account other than root and allow that account to run the "sudo passwd" command. If the sudo configuration cannot be changed, another option would be to modify the UNIX target application by changing the Privilege Elevation Command setting in the Script Processor section. A dummy "echo ;" command like shown below would allow the update script to work, although it would then work only for the root account and not for accounts that would need elevated privileges to change another account's password. This change would not impact the ability of any account to change its own password.
It is also possible to configure a custom Update Credentials script for a given UNIX target application, but that would have to be done by engaging CA support or services and should be considered as a last resort only.